This has been a tough week. I’m not the first to compare the galloping sense of dread and horror I feel upon the elevation of a racist, sexist, xenophobic demagogue to the White House to the feeling many of us experienced after 9/11: On a visceral level, we know a terrible thing has happened.
Others have compared it to the sense of having lost a loved one, and that fits too. The loved one in this case is the country we thought we knew, which turns out to be a meaner, shittier place than some of us (namely, me) previously acknowledged.
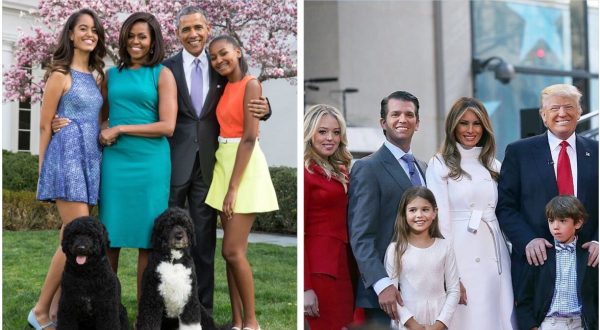
People who are less white, wealthy or straight than I am knew it all along, of course. My kid is gay. On November 9th, I apologized to her for not preparing her more thoroughly to live in a dystopian shithole, because I didn’t see this coming, didn’t think America was capable of replacing Barack Obama with Donald Motherfucking Trump. Biggest downgrade of all time!
She said, “That’s okay, Mom. I never had your faith anyway.” Well, what do you say to that? Fuckifino.
But through it all, there’s been one bright spot in the shitstorm, and that’s right here, this blog, Balloon Juice. We’ve vented our spleen, bucked each other up, traded ideas on how to cope.
I just wanted to thank you for that, and to let you know I appreciate you. Well, not all of you. There are a few people whom I’d relish seeing roasted on a spit in hell with Demonic Newt Gingrich in a red velvet banana-hanger poking at them with a molten-red hay fork — you know who you are!
But with that exception, thank you. From the bottom of my bruised and battered heart.