Throughout the comments since last night’s breaking news regarding Robert Mueller’s Special Prosecutor’s investigation into Russian interference in the 2016 elections there is a lot of confusion and speculation, informed and uninformed, about what is actually going on. I wanted to make what I think is an important, but often forgotten point: Mueller’s investigation is rooted in/an outgrowth of a joint counterintelligence investigation.
Joint Publication 2-01/Joint and National Support to Military Operations defines counterintelligence as:
Counterintelligence (CI) uses collection techniques that are similar to HUMINT, but CI targets those entities that are targeting friendly forces, a more narrow focus than HUMINT. Nonetheless, exploitation of data collected by CI assets can yield information critical to I&W and force protection. Service component CI elements conduct CI collection using liaison; elicitation; passive collection; review of open sources; military CI collections; and screening, interviews, and debriefing of displaced persons, defectors, refugees, and US persons with access to information of CI interest. Additionally, law enforcement information and suspicious activity reports are important sources of information that need to be processed, exploited, and fused with other CI sources. Processing of CI information primarily involves report preparation by collection activities at both the joint force and component levels. At the joint force level, this processing may also be accomplished within the J-2X*.
For more detailed information regarding CI processing, exploitation, and reporting, see JP 2-01.2, Counterintelligence and Human Intelligence Support to Joint Operations.
Lawfare has an excellent two part run down of counterintelligence in regard to Mueller’s mandate as the special prosecutor by Aditya Bamzai. Professor Bamzai explains in part one:
Counterintelligence investigations are different from criminal investigations in several ways. For one thing, the goal of a counterintelligence investigation may be different from, and perhaps broader than, a criminal investigation. A criminal investigation would ordinarily pursue allegations of criminal conduct. A counterintelligence investigation, by contrast, may pursue allegations of “coordination” between U.S. persons and foreign hackers that may be unseemly and problematic if true, but potentially not criminal—such as, to use Professor Kent’s example, the possibility that a person within the United States coordinated to distribute material previously hacked by agents of a foreign government. As the Attorney General’s Guidelines for Domestic FBI Operations explain, the FBI is “not limited to ‘investigation’ in a narrow sense, such as solving particular cases,” but may also collect information to support “broader analytic and intelligence purposes.” In the case of the FBI, the line between counterintelligence and criminal investigations may not be a bright one. “In many cases,” as the Guidelines put it, “a single [FBI] investigation will be supportable as an exercise of a number of these authorities—i.e., as an investigation of a federal crime or crimes, as an investigation of a threat to the national security, and/or as a collection of foreign intelligence”—because the FBI has a role in enforcing both criminal law and “in collecting foreign intelligence as a member agency of the U.S. Intelligence Community.”
There’s a lot more at the link, but this, I think, is one of the most important portions for everyone to get their heads around. Mueller inherited the joint counterintelligence investigation that had begun during the summer of 2016 into Russian active measures and interference in the 2016 election. This means that Mueller and his team in the Special Prosecutor’s office have access to the full range of US, allied, and partner intelligence and counterintelligence related to the issues he’s investigating. It is this material that forms the bases of FISA warrant requests, not political oppo research like Fusion GPS’s Steele dossier.
In seeking to bring charges, which are not always the focus or outcome of a counterintelligence investigation, Mueller has to navigate from the world of intelligence and counterintelligence, from the classified world of need to know and special access programs to information that can be brought before a grand jury. This means that while Mueller, his team in the Special Prosecutor’s office, and those on the joint counterintelligence task force he inherited know the full depth, breadth, and scope of what happened, how it happened, why it happened, where it happened, and who it happened to it doesn’t mean he can just curate that into a compelling narrative and bring it to the grand jury. Like everyone else with a clearance and access he has to protect not just the information, but the sources and methods that were utilized to get the information. This means that whatever information he brings to the grand juries he has access to, and whatever charges he brings, are going to have to fit within the body of Federal criminal law.
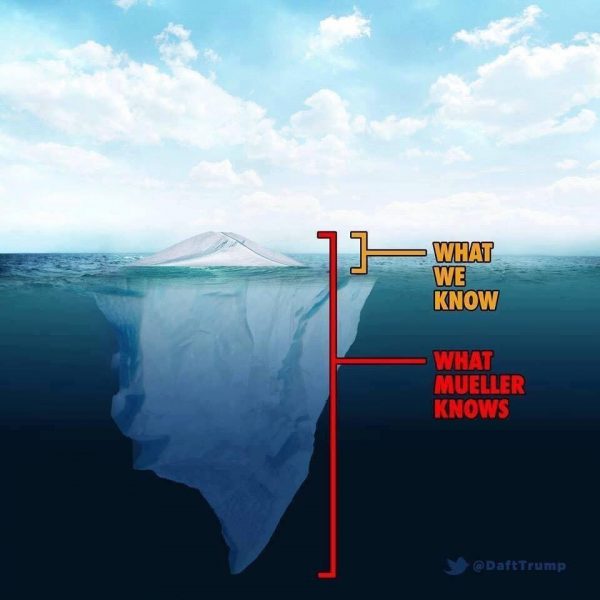
As a result there is a lot of speculation that what he’s doing looks like a white collar investigation and prosecution or one of organized crime. And this may be true as far as appearances go. But it is true in that he and his team have to find evidence that can be presented to the grand jury and then utilized in a trial to prosecute those who are the target of his inquiries and the joint counterintelligence task force. We may never see a charge of espionage, because while it certainly happened with the hacking of Podesta’s emails, the DNC, the DSCC, and the DCCC, as well as similar hacking of GOP organizations and officials, Mueller may not be able to make that case without divulging sources and methods. Instead he’s got to find another way to get at those who engaged in these activities through more mundane charges. Hence all the speculation about leveraging Treasury’s Financial Crimes Enforcement Network (FINCEN), as well as other investigations into financial and business irregularities into Manafort, Flynn, etc. What we’re going to see play out in public – as a result of indictments and prosecutions – is really just a bit of what has actually happened and what Mueller and his team know. In this case the meme is very, very accurate.
* The J-2X is the staff element of the intelligence directorate of a joint staff that combines and represents the principal authority for counterintelligence and human intelligence support. See also counterintelligence; human intelligence. (JP 2-01.2) Adam here: J stands for Joint, 2 is the numerical code for the intelligence section in a US military unit, and the X here is referring to the counterintel and human intel personnel.

Mike J
Lizzy L
Thank you for this clarification, Adam. Extremely helpful. Two questions:
1) May I/we share this analysis (i.e. friends, FB)
2) If it is shared, do you wish it to be attributed to you?
Corner Stone
Orange jumpsuits shine just as brightly for money laundering as they do for treason.
Adam L Silverman
@Lizzy L: You can share it. If you need to back up who I am, you can use the following short bio:
Adam L. Silverman is a national security professional currently working as a consultant within the US defense sector. He has held term civil servant appointments through the Intergovernmental Personnel Act at the Office of the Secretary of Defense for Security Dialogue (JUN 2014-AUG 2014) and as the Cultural Advisor at the US Army War College (2010-2014). He has served, under temporarily assigned control, as the Cultural Advisor for US Army Europe (DEC 2013-JUN 2014), US Army Institute for NCO Professional Development and the Commandant of the US Army Sergeant’s Major Academy (NOV 2013-JUN 2014), III Corps (JAN 2012-SEP 2012), and Civil Affairs Branch (OCT 2012-OCT 2013). From OCT 2007 to NOV 2008 he served as the contracted Cultural Advisor to the 2nd Brigade Combat Team/1st Armored Division/Team Leader and Field Social Scientist of Human Terrain Team Iraq 6 and was deployed with the brigade in Iraq in 2008. He has provided support to CENTCOM, SOCOM, AFRICOM, EUCOM, US Army Europe, US Army Central, US Army Africa, US Army Special Operations Command, US Army Office of the Provost Marshal General and US Army Corrections Command, I Corps, III Corps, XVIII Airborne Corps, V Corps, 1st Armored Division, 101st Airborne Division, the 4th Brigade Combat Team/101st Airborne Division (Air Assault), the Department of State’s Near East and South Asian Director, the Department of State’s Office of Provincial Reconstruction Iraq, the Department of Homeland Security, and the Deputy Commanding General of the United Nations Mission in South Sudan.
Ruckus
@Adam L Silverman:
That’s longer than my entire CV and I spaced it out and used big type.
hueyplong
I prefer money laundering. Seems less “political” than treason to relatively low information but relatively objective observers. Seems more like rooting out crooks.
And these guys are most definitely crooks.
Should help for midterms.
Smiling Mortician
@Adam L Silverman: Right after I read this, my CV gave me serious side-eye, shook its head, and walked away.
(((CassandraLeo)))
Thanks for keeping us up to date with this stuff. I don’t think I can even express how helpful posts like this have been at cutting through the noise, and I suspect you’ve averted at least one freakout on my end.
@Ruckus: @Smiling Mortician: Yeah, I feel like I’ve wasted an awful lot of my life after seeing that.
Smiling Mortician
@Ruckus: Come sit by me.
Adam L Silverman
@Ruckus: @Smiling Mortician: My full CV, single spaced, but with section breaks runs almost 30 pages. And I’ve left off about a half dozen presentations at academic meetings only because I can’t be bothered to go back and look up the titles of the talks.
NotMax
Rs are quite big on accusing people (often blithely) while invoking the phrase “in wartime.”
Any quick thoughts on how or if that same invocation may come into play re: Mueller’s portfolio? And yes, am cognizant that the vast majority of laws on the books do not make distinction between times of war and non-war.
Adam L Silverman
@hueyplong: I’m not arguing against it, just explaining what is going on.
(((CassandraLeo)))
@hueyplong: ¿Porqué no los dos?
germy
Adam L Silverman
@Ruckus: @Smiling Mortician: @(((CassandraLeo))): I only provided the bio because one of our other readers/commenters posted one of the pieces I did on what the 3rd SF group guys were doing in Niger on FB and got some guy who makes tubas in Tennessee show up and argue I didn’t know what I’m talking about because there was no bio. Personally that doesn’t bother me, but it upset that reader/commenter and I’m trying to save Lizzy L some of the same heartburn.
Also, I did a lot of temporary duty assignments for the better part of five or six years. My first year at USAWC I was on the road, on average, one week a month. The 13 months after I got back from Iraq I was on official travel at meetings and working groups and planning meetings 3 out of every 4 weeks on average.
JPL
Trump is going to release the rest of the files on JFK.
https://twitter.com/RealPressSecBot
He’s desperate to change the topic.
(((CassandraLeo)))
@Adam L Silverman: Nah, I understand perfectly, and to be honest, it’ll help me to have that bio whenever I post your stuff elsewhere in the future. It really does make me realise how little I’ve done with my life though. Hopefully I’ll have finished a book by the end of the year, though, which I guess is more than most people can claim to have done.
JPL
@germy: I ruled out Manafort because he’s not a flight risk. The Manafort team already knew they were in danger of indictment. Hopefully he flipped.
trollhattan
@JPL:
Time to send Pence to stomp out of a football game. Works every time.
Marcopolo
Thanks for the reality check, Adam. At this point, I am just glad to see charges now filed. It’s the beginning and I hope there is lots and lots more to come. From what I’ve seen since the inauguration I don’t have a lot of trust that the vast majority of the current Federal gov’t and bureaucracy are working with the best interests of the average American in mind, but Mueller hopefully does. Also, I don’t find I have a lot of desire to speculate on what’s going to happen. I’d rather put that time and energy into putting pressure on my electeds to do the right thing in regards to kids relying on CHIP for healthcare or DACA protections to stay in the country. And keep my expectations low so I am pleasantly surprised by what happens.
Hoping everyone is having a bang up pre-Halloween weekend.
Corner Stone
@germy: Manafort lies as easily as his lips move. Just flat out lies to the person’s face.
WTS, the teasing that JarJar is in the immediate crosshairs is really good.
Alternative Fax, a hip hop artist from Idaho
And given all that, this investigation has moved at the speed of light. These people, as some on the Twitters say, are #FINCENfucked. Financial crimes indictments will indeed sound much less political than espionage charges, and will not risk compromise of sources and methods. Nor will FARA (Foreign Agent Registration Act) violation prosecutions, and some of those violations are quite clear. There are some apparent FARA violations by Dems, e.g., Tony Podesta.
bystander
We have only heard that Manafort was warned he would be indicted and they conducted the surprise search of his house. So, while I would truly rejoice if it were Jared, I’m expecting it to be Manafort, whether he expects it or not.
JPL
@trollhattan: Tomorrow. He’ll probably go the Texans game.
(((CassandraLeo)))
@Corner Stone: As frequently? Sure. As easily? I dunno. He’s really, really bad at it. You can hear the flop sweat in his voice.
Sam
The problem with the undersea part of the iceberg is that it may not be legally actionable. That is why our broken political process is so important. The Gang of 8 could certainly access all relevant intel and make informed decisions about the proper political course.
My disappointment is that this does not seem to be happening. Alternatively, there isn’t enough there to convince our representatives to take politically fraught actions.
The net result of this political dysfunction is that a lot of intel may just be of historical interest, Muellers job is difficult, and bad actors may in fact never face any penalty at all. It will be interesting, for sure.
Adam L Silverman
@(((CassandraLeo))): I was very fortunate to have a chance to have some adventures. But honestly a lot this stuff is mundane. Like answering requests for information on specific issues by providing a strategic assessment. Or sitting in a week of death by powerpoint meetings.
germy
Roger Stone just had his twitter account suspended.
Adam L Silverman
@Alternative Fax, a hip hop artist from Idaho: Yes and no. In terms of being under Mueller’s supervision it’s been five months since he was appointed as Special Prosecutor. But this investigation is almost 18 months old total.
(((CassandraLeo)))
@Adam L Silverman: I figured a lot of that stuff was less exciting than it sounds. Still, it’s probably a lot more rewarding than the seven and a half years I spent in retail, and it gives you a lot more fodder for a CV.
@germy: And nothing of value was lost.
trollhattan
@JPL:
Heh, too bad the Texans are playing away instead of at their home penitentiary. I’d love to see the welcome Pence would receive in Seattle.
Adam L Silverman
@germy: He’s panicked. And he’s got good reason to be.
Lizzy L
@Adam L Silverman: Thank you. If anyone questions your level of knowledge, I will share the CV in private.
Cermet
Can a Grand Jury only indict (sic previous) one person or can it do numerous people for similar but different parts of the overall case?
Ruckus
@Adam L Silverman:
No worries, I fully understood the context, but other than 3 yrs in the navy, my sum total of working within the federal government is paying my taxes. I did a fair bit of sub contracting in the military aerospace segment in the 90s and the paperwork/paper trail reminds me of that. A little bit. Also over 20 yrs of my CV is two lines, describing the businesses I owned. Takes 2 words to describe the jobs, president, owner. Done.
Adam L Silverman
@Lizzy L: However you want to play it.
(((CassandraLeo)))
@Adam L Silverman: As loathsome as Stone is, the people I really want taken down by this investigation (besides the president* and other prominent GOP officials) are the Mercers. I hate to criticise people’s appearances (apart from Ted Cruz’, because really), but they even look creepy.
Dorothy A. Winsor (formerly Iowa Old Lady)
@germy: Hee. It’s probably a good thing, but we lose the entertainment value.
What reason was given for the suspension?
Adam L Silverman
@(((CassandraLeo))): I would think, at least in terms of counterintel, they’re in a fair amount of trouble.
trollhattan
@germy:
Heh. Did he use Nixon as an avatar, or just the thing atop his head?
germy
@Dorothy A. Winsor (formerly Iowa Old Lady):
Adam L Silverman
@germy: @(((CassandraLeo))): @Dorothy A. Winsor (formerly Iowa Old Lady): Make that he’s not coming back:
germy
@trollhattan: I can’t believe a member of the watergate gang is still around damaging our country. I was a teenager when they were first busy, and now I’m almost 60. I wish they could have taken up fly fishing instead.
(((CassandraLeo)))
@Adam L Silverman: That might be the best news I’ve heard all day. Stone being perma-banned from Twitter is just icing after that.
HeleninEire
@Ruckus: Did you see my thank you a few threads back? I am always backed up a few threads cuz I’m in Ireland. Thank you and good luck to you.
A few threads??? Oh holy hell. The clock turns back tonight. A week before America.
p.a.
So Silverman, if that is your real name, as a current USG consultant, has your IRS audit been scheduled yet? First audit ever authorized via Twitter…
Adam L Silverman
@p.a.: No. I’m good. Thanks for checking though.
Jay S
@Ruckus:
Just shows he can’t keep a job :-)
trollhattan
@germy:
Yup, between those and the never-went-away Reaganites it’s been an endless loop of bad ’70s and ’80s sitcoms, which are as unfunny today as on first broadcast.
Arthur Laffer, everybody!
RobertDSC-iPhone 6
@Adam L Silverman:
I have decided that I want to be Adam when I grow up.
Baud
@Adam L Silverman: What was the reason given? Harassment?
germy
@trollhattan: Do they drink tiger blood for breakfast? I’m barely left standing, and these guys seem younger and stronger than ever.
germy
Washington Post has been curiously silent on this matter. Are they sitting on something? Waiting until Monday to report?
Adam L Silverman
Submitted without comment:
trollhattan
@germy:
It’s the Cheney soul-for-immortality thing, they got a volume discount.
Adam L Silverman
@Jay S: Very, very true.
Adam L Silverman
@RobertDSC-iPhone 6: No you don’t. Trust me.
HeleninEire
Fitzmas. Patrick Fitzgerald broke my heat.
Adam L Silverman
@Baud: I have no idea.
debbie
@germy:
Maybe he knows he’s safe because he flipped on Jared.
germy
@Adam L Silverman: I like how they’re all running their mouths while they’re led away. Except for Spicey, who seems to be texting. Did Spicey turn them all in? (And Trump, who doesn’t seem to know what’s happening…)
Jay S
@Baud: I’m pretty sure they only tell the public it’s a TOS violation, like the screen grab shows. From what others have said they don’t give specifics to the people they TOS out either,.
Fair Economist
@Corner Stone:
Indeed. Besides that, he’s not particularly likely to known who’s being indicted – they wouldn’t give him advance notice. So Manafort’s claims are dishonest claims by the ignorant – i.e., uninformative.
germy
@debbie: Why is ivanka grinning in the car?
Timurid
@germy:
It’s become a Friday night ritual on Twitter to spend the early hours speculating about the Big Story that WaPo is about to dump and the late hours dancing to the cricket orchestra.
Jay Noble
@Cermet: Same question here – Can an indictment be for more than one person? It takes few people to make a conspiracy, so son’t you get to prosecute them all together?
Corner Stone
@germy: She ratted everyone out to save her skin. Now she has the keys to everything while they are all doing hard time.
Adam L Silverman
@Cermet: @Jay Noble: Yes, it can be for one or more than one person. From the wording of the CNN story, the speculation is there may be more than one in this first batch of indictments. We’ll have to wait till next week to find out though.
JPL
@Adam L Silverman: I love that. It was on the boss’s twitter feed, and I have watched it several times.
Jay S
@Jay S: But if I had to guess some of Stone’s tweets from last night looked like an attempt to incite violence against specific CNN reporters.
HeleninEire
@RobertDSC-iPhone 6: Yeah me too, But Adam is young enough to be my son So, when I grow up I wanna him to be my son. Oh hey what?
Ruckus
@HeleninEire:
I did see it.
No worries, we are a mini society, we need to have each others backs. I had hoped when I wrote the comment that you referenced that I hadn’t gone overboard.
ETA according to my calendar daylight savings change is next Sat.
germy
@Jay S: Gorka called for Hillary’s execution.
Adam L Silverman
@germy: Gorka is a moron. I’m the actual national security professional that Gorka has been pretending to be.
Ruckus
@RobertDSC-iPhone 6:
Can you type at 80 words a minute? Or faster? Cause otherwise you won’t make it.
Cheryl Rofer
@Adam L Silverman: The wording is that arrests may be made “as soon as Monday.” Part of that is legal carefulness, but it also may mean that we won’t see arrests immediately.
Jay Noble
I’ve read several stories today (and here for some time) that this is too soon, that it will take awhile, 2 years for watergate, etc. But are we forgetting that we live in the electronic age? This isn’t (necessarily) people digging through reams of paper only to find out the next ream is in another warehouse. We are talking emails and texts and stuff that can be searched in seconds. I think they’ve had the info for some time and have just getting things lined up to fall properly.
CaseyL
@Adam L Silverman: The Mercers? The Mercers might be in a fair bit of trouble?
That warms the cockles of my heart just as much as Trump & Assoc. being in Mueller’s crosshairs.
Adam L Silverman
@Cheryl Rofer: Yep. Gonna have to order more popcorn!
Jay S
I haven’t seen the Gorka stuff, but usually Twitter is hard to move on anything that can be constrained as vague or not true threats. I think Stone may have crossed a line if not a legally actionable threshold. But then Twitter is pretty notorious for inconsistent ban/not-ban decisions.
Germy https://balloon-juice.com/2017/10/28/just-a-quick-note-on-the-mueller-investigation/#comment-6608527
Suzanne
@germy: If it’s Jared, I think I may instantly have to jump on my husband.
Ruckus
@Jay Noble:
Also as Adam noted this investigation has been on going for 18 months, not just the last 5.
? ?? Goku (aka The Hope of the Universe) ? ?
@Jay Noble:
That and the fact that as Adam pointed out, Mueller inherited the investigation from the FBI which began last summer, so he had a head start too. Having access to the ongoing intragency counterintelligence task force has help immensely too I’m sure. Another reason may be that these are low-level (relatively speaking) arrests to get to higher-ups for more information that will help further their case.
Adam L Silverman
@Ruckus: And the investigation into Manafort has been on and off since 2014.
Adam L Silverman
germy
@Jay S: Gorka said it on TV.
Adam L Silverman
debbie
@germy:
Grinning, or gritting her teeth? ?
Cheryl Rofer
Loving that Roger Stone got bounced from Twitter.
I keep boggling at Stone and Roy Cohn, two of Nixon’s slimiest, persisted with Trump.
cynthia ackerman
Thank you, Adam.
You are a national treasure.
germy
Adam L Silverman
@Cheryl Rofer: Manafort was part of that group that Cohn mentored.
Adam L Silverman
@cynthia ackerman: You’re welcome.
This also explains why Nicholas Cage keeps showing up at my house.//
Another Scott
Thanks for the writeup. You, and the Lawfare guy, may be right.
It seems weird to me to have that interpretation of Rosenstein’s letter and 28 CFR 600.4+ though. Why wasn’t Rosenstein’s letter more explicit about the scope of the investigation if it’s primarily or explicitly a CI investigation?
I get the backstory (at least as I understand it) – Comey was nominally the head honcho overseeing the very broad CI investigation (as his job as head of the FBI). But presumably the vast, vast majority of the work was being done by CI teams, not by Comey’s office. Why would Mueller’s maximum role there – the figurehead kept informed – be any different? The rest of the Muller team (at least what we’ve heard about the appointments) seems to be much more involved in looking at money laundering and dodgy real estate deals and public corruption prosecutions – not ex-spooks. Transfers within the FBI, etc., might not get any public announcement though – I dunno.
Rosenstein’s letter didn’t (it seems to me) appoint him to be quasi-FBI-director. His mandate is limited. It would make sense to me for the CI stuff to be continuing under the previous teams but for them to be reporting to Mueller (and Rosenstein) rather than Sessions. But Muller’s main mandate is looking at Russian interference in the 2016 election and related things. Presumably lots of that can be made public without compromising “sources and methods” and all the rest.
I agree with you that a CI investigation is something that is very complex and there are lots of moving parts that may not lead to prosecutions in court. The money laundering, etc., etc., seems to be a more fruitful path for public prosecutions – if the rumors and previous reporting are accurate, of course.
So, we may be on in the same book, but not yet on the same page. We’ll see how it turns out. Or not! :-/
My $0.02. Thanks.
Cheers,
Scott.
Jay S
@germy: Ah, I did hear about some of that as part of the squid ink that has been trying to cloud the Mueller investigation. The joke will be on us when Mueller has Hillary arrested on Monday. /jk
Gin & Tonic
@Fair Economist:Don’t forget that Manafort was the subject of a no-knock warrant. They were in his house while he was asleep, and he didn’t know about it until they came in his bedroom. I don’t know about the rest of you, but that would be pretty serious fear of God stuff to me. I don’t think he should be counting any chickens this weekend.
Spaneil
Has anyone heard or seen from Kellyanne Conway lately? She usually is the Shield of Misdirection, with +4 abilities to redirect barbs back onto the thrower, with a news story like this.
Cheryl Rofer
Adam L Silverman
@Cheryl Rofer:
1:
2:
cynthia ackerman
@Adam L Silverman:
Now that’s a sad commentary …
//Richie Aprile
Adam L Silverman
@cynthia ackerman: I need to get out more often…
Adam L Silverman
@Another Scott: It is a hybrid investigation. Criminal layered on top of CI. Hence my explanation of Mueller having to find ways to bring charges that don’t violate classification or give up sources and methods.
J R in WV
Adam, when I think of how much less informed and more ignorant I (we all) would be without your willing education about things that can be known by the public, but which are usually kept in the shadows rather than out where people can look at them.
Thank you!! Now I’ll read the other comments, which are often also educational and interesting, or not. Tomorrow we’re going to a memorial service for a long time friend, activist, environmentalist and organizer who fought briefly and bravely with Fuck Cancer!
So there’s more emotion flowing right now than usual, between her death and the “news” which may or may not be real, about sealed indictments. Hang in there, everyone! Monday’s coming, and so is winter.
BC in Illinois
@Sam:
And while it will be emotionally gratifying — and essential for our political system — to see the majority of the Trump campaign / crime operation incarcerated, the final steps toward cleansing the White House depend on our “broken political process.”
I have been reading Charles L Black Jr’s Impeachment: A Handbook Written in 1974 for the time of Nixon, re-issued in 1998. Still relevant.
To sum up an 80-page handbook. You don’t remove a president because he’s a shitty president. You don’t remove him because he’s unpopular on incompetent. You don’t even need, on the other hand, to conclude that he has committed an indictable criminal offense.
We should — and must — remove a president whose
(emphasis mine)
The preface talks about “misdeeds . . . so gross and malignant as to warrant undoing a national election.”
This is what I want from the Mueller report, when it finally comes to light. Not a side-argument on whether this action or that action is criminal. But a clear picture of what was done, leading to a “general societal view” that Donald Trump in the White House is — by his very actions — intolerable, and warrants being removed, by an overwhelming national consensus.
There is no such thing, in 2017, as a “general societal view.” On anything. We need to create it. We need to fight out this fight with our eyes open to life in this nation after the fight is over. When the Mueller report comes out, it will not be the “beginning of the end”; it will not even be the “end of the beginning.” It will be a flash of sunlight onto a land where will need to be able to convince our neighbors that “You see that? That’s light!”
I look forward to the day when we can talk in terms of Lincoln’s 2nd Inaugural: malice toward none, finish the work, bind up the wounds, create a just and lasting peace. I think that the work of Robert Mueller will bring us up to the point of the 1st Inaugural — time to do what’s necessary to hold us together.
Nothing will end on Monday.
Adam L Silverman
@J R in WV: My sincerest condolences for your loss.
The Very Reverend Crimson Fire of Compassion
@germy: hell, this shit predates Nixon. Roy Cohn was Joe McCarthy’s aide, and Trump’s mentor. I haven’t done the research to connect the dots, but I’m willing to bet there’s a line of apostate succession running all the way back to the traitors of the Confederacy, if not before. As the hippie rabbi taught us, “The poor ye have always with you.”
Uncle Ebeneezer
@(((CassandraLeo))): For what it’s worth, you help this cis/het/white man better understand privilege, oppression and how they tie into politics on a regular basis, just by reading your comments, here and at LG&M (and probably other places too, that I’m forgetting.)
(((CassandraLeo)))
@Uncle Ebeneezer: Thank you kindly. FWIW, most of my comments are (with my most frequented community first) at LGM, here, and at Wonkette (where comments are not allowed); I also make occasional excursions over to Edroso’s place, though I mostly lurk there, so the odds that you’ve forgotten somewhere probably aren’t that high. I’m glad to know that people are learning things from my comments, though.
Origuy
@Ruckus:
It’s this weekend in Europe. Just another reason to hate Daylight Savings Time. Computer systems have to be constantly updated to keep up with the changes.
J R in WV
@Adam L Silverman:
Thanks Adam, it’s a small and tight community as you can imagine. Intellectuals and progressive activists are a tiny minority here in SW WV. You live in FL so you know what I’m talking about… after 2 or 3 decades you know people you see rarely – a few times a year – better than people who live right down the road.
I’m old enough to have lost all my grandparents and parents and aunts and uncles, and are starting in on cousins. Our friends are the family we choose. We have blood relatives we won’t associate with, and friends we can’t afford to lose.
I have to wish Mueller, and his associates, the best of luck. I expect they are in real physical danger, actually. But they are professionals, and educated and trained in dealing with those threats.
And you too are trained, and have big dogs. Take care!
SgrAstar
@Adam L Silverman: ummmm…I’m trying to decide whether I need to see the long version, Adam. Nice!
Ruckus
@Origuy:
Thanks. Wondered if that was it.
I actually don’t mind so much. I drive due east in the morning and of course due west in the evening. This time of year, directly into the low sun both going and coming. Changing the time helps a lot. And is the best and only reason I can see for doing it.
Ruckus
@J R in WV:
Well other than being the oldest cousin that anyone talks to we are in the same place. The only cousin who is older is in a cult and no one talks to that one. And many of the others have moved around the country enough that most of us been unable to stay in touch.
Adam L Silverman
@SgrAstar: Again:
1) Only included because last week someone else here shared something I wrote on FB and had someone show up and try to trash it because he had no idea who I was.
2) It sounds way more impressive than it is.
NotMax
@Adam L. Silverman
Most things do.
;)
Lurking Canadian
I remain uncomfortable with this line of reasoning. The US is, in the end, a democracy. Yes, representative republic, but the power of sovereignty is supposed to reside in the people.
Right now, the republic is in peril, and the people don’t have a clue why, because the national security establishment has decided that it is more important to keep secret sources and methods than to tell the people, who in the final analysis, are their boss and pay their salaries, just exactly what is going on in their country.
There’s a disturbing paternalism to it. The US is allowed to have only the degree of popular sovereignty that the national security establishment thinks proper.
J R in WV
@(((CassandraLeo))):
Oh, really now? That’s funny among those who know it’s a joke… but here where people who have never commented at Wonkette you need to be a little more up front, ;-)
J R in WV
@Lurking Canadian:
And I agree with you. Often, when the nation is not at stake, surely methods and sources are important to protect. Today, the nation is very much at stake, and our enemies are at the center of the nation’s power. Methods and sources are only as important as the proof they provide of the guilt of the traitors!
(((CassandraLeo)))
@J R in WV: I thought it was fairly well known, and that the sentence structure would give it away for anyone who didn’t already know it: “my comments… at Wonkette (where comments are not allowed)”. Ah well. :p
Another Scott
@(((CassandraLeo))): Too subtle. ;-) Wonkette isn’t a daily stop for me, but they do have hundreds and hundreds of comments on threads, so I kinda wondered what you were getting at. ;-)
Cheers,
Scott.
Sister Golden Bear
@Adam L Silverman: A girl can dream…
Le Comte de Monte Cristo, fka Edmund Dantes
@Adam L Silverman:
You totally have to read “Dave vs The Monsters” (written by John Birmingham) to see what happens when a senior Human Terrain Specialist gets assimilated by the Monsters…
Le Comte de Monte Cristo, fka Edmund Dantes
@Adam L Silverman:
You totally have to read “Dave vs The Monsters” (written by John Birmingham) to see what happens when a senior Human Terrain Spec!alist gets assimilated by the Monsters…
Le Comte de Monte Cristo, fka Edmund Dantes
@Alternative Fax, a hip hop artist from Idaho:
I’d like to think that this will start curbing the 10-15 yr proliferation of the “international political consultant” title.