NBC News is reporting out that the US Government has taken steps to prepare to counter-strike a Russian cyber attack on election day next week.
U.S. military hackers have penetrated Russia’s electric grid, telecommunications networks and the Kremlin’s command systems, making them vulnerable to attack by secret American cyber weapons should the U.S. deem it necessary, according to a senior intelligence official and top-secret documents reviewed by NBC News.
American officials have long said publicly that Russia, China and other nations have probed and left hidden malware on parts of U.S critical infrastructure, “preparing the battlefield,” in military parlance, for cyber attacks that could turn out the lights or turn off the internet across major cities.
It’s been widely assumed that the U.S. has done the same thing to its adversaries. The documents reviewed by NBC News — along with remarks by a senior U.S. intelligence official — confirm that, in the case of Russia.
U.S. officials continue to express concern that Russia will use its cyber capabilities to try to disrupt next week’s presidential election. U.S. intelligence officials do not expect Russia to attack critical infrastructure — which many believe would be an act of war — but they do anticipate so-called cyber mischief, including the possible release of fake documents and the proliferation of bogus social media accounts designed to spread misinformation.
And
Brown and others have noted that the Obama administration has been extremely reluctant to take action in cyberspace, even in the face of what it says is a series of Russian hacks and leaks designed to manipulate the U.S. presidential election.
Administration officials did, however, deliver a back channel warning to Russian against any attempt to influence next week’s vote, officials told NBC News.
The senior U.S. intelligence official said that, if Russia initiated a significant cyber attack against critical infrastructure, the U.S. could take action to shut down some Russian systems — a sort of active defense.
Retired Adm. James Stavridis, who served as NATO commander of Europe, told NBC News’ Cynthia McFadden that the U.S. is well equipped to respond to any cyber attack.
“I think there’s three things we should do if we see a significant cyber-attack,” he said. “The first obviously is defending against it. The second is reveal: We should be publicizing what has happened so that any of this kind of cyber trickery can be unmasked. And thirdly, we should respond. Our response should be proportional.”
Finally,
One problem, officials say, is that the doctrine around cyber conflict — what is espionage, what is theft, what is war — is not well developed.
“Cyber war is undefined,” Brown said. “There are norms of behavior that we try to encourage, but people violate those.”
For further reading if anyone is interested, here’s the link to Joint Publication (JP) 3-12(R)/Cyberspace Operations. JP 3-12 covers all the Joint Force doctrines and concepts for cyberspace operations. Here’s the link to the US Army Cyber Center of Excellence (COE)* doctrine and concepts brief for those that like death by powerpoint. Finally, here’s the link to a very interesting monograph on cyberspace operations published by the US Army War College’s Strategic Studies Institute (full disclosure: I know the author, he was on the faculty of USAWC during the first two years of my assignment there).
* The Army uses Center of Excellence for the overarching Branch commands at their Professional Military Education (PME) schools. These are not traditional, civilian academic Title VI Centers of Excellence.

Viva BrisVegas
More for its resonance than its relevance:
Remember, remember!
The fifth of November,
The Gunpowder treason and plot;
I know of no reason
Why the Gunpowder treason
Should ever be forgot!
Guy Fawkes and his companions
Did the scheme contrive,
To blow the King and Parliament
All up alive.
Threescore barrels, laid below,
To prove old England’s overthrow.
But, by God’s providence, him they catch,
With a dark lantern, lighting a match!
A stick and a stake
For King James’s sake!
If you won’t give me one,
I’ll take two,
The better for me,
And the worse for you.
A rope, a rope, to hang the Pope,
A penn’orth of cheese to choke him,
A pint of beer to wash it down,
And a jolly good fire to burn him.
Holloa, boys! holloa, boys! make the bells ring!
Holloa, boys! holloa boys! God save the King!
Hip, hip, hooor-r-r-ray!
Karmus
We do live in interesting times.
Smedley Darlington Prunebanks (Formerly Mumphrey, et al.)
I’m glad they’re on top of this. The only thing is, what if it isn’t the Russians who try something? What’ll they do if the F.B.I. tries to black out whole cities or something? And, yes, I am kidding about this–more or less…
Boussinesque
Well shit. Hopefully the Russians will take the hint–what kind of odds do you place on this…dissuading them, Adam? Or that transparency on the part of the administration will help mitigate the impact of any Russian cyber-ops?
dmsilev
I assume this is being made public as a not-so-subtle warning to the Russians to back off.
gf120581
@Smedley Darlington Prunebanks (Formerly Mumphrey, et al.): I think we need to remember that it’s not the whole FBI out to get Hillary. It seems like the main culprits are a handful in the NY office for the pettiest of reasons (pissed over the Eric Garner case, seriously?!!!).
Pogonip
@Smedley Darlington Prunebanks (Formerly Mumphrey, et al.): In that event, everyone’s invited to my house; we have several of those super-bright flashlights.
Walker
Time for the assault on the Kirensk computer nexus.
Omnes Omnibus
@dmsilev: There is no other reason to make it public.
Adam L Silverman
Breaking news in the next post. And yes, I know I just bigfooted myself!
SiubhanDuinne
@Viva BrisVegas:
Don’t think I have ever seen the entirety of the Guy Fawkes doggerel. The first lines, yes indeed. And I have somewhere run across
A rope, a rope, to hang the Pope,
A penn’orth of cheese to choke him,
A pint of beer to wash it down,
And a jolly good fire to burn him.
but had no idea it was from the same poem.
Thanks for this! And it does seem to chime with our situation in the U.S. today.
redshirt
@Pogonip: LAN party at my compound!
Bill E Pilgrim
Good lord.
This is all kind of like the movie War Games, but in reverse. Or something.
Back then everyone was freaking out watching online or digital activity only in case it was reflecting physical attacks. If it was just online, then whew, all was okay. Now everyone is staring at the screens and it’s the online activity itself that’s the danger.
Adam L Silverman
@Smedley Darlington Prunebanks (Formerly Mumphrey, et al.): The FBI is only responsible for any crimes committed on US soil, though they do have liaison officers in almost every US embassy. Cyberspace Operations are under the purview of US Cyber Command, which is part of US Strategic Command:
https://www.stratcom.mil/factsheets/2/Cyber_Command/
Adam L Silverman
@Boussinesque: This is the public warning. I’m sure more private warnings have also been issued. We’ll just have to wait and see just how far Putin wants to push things.
Smedley Darlington Prunebanks (Formerly Mumphrey, et al.)
@Adam L Silverman: No, I meant what would they do if it’s the F.B.I. blacking out cities here. And, yeah, it’s still a joke… Kind of…
Carlo Graziani
Retaliating in kind to this sort of cyber-warfare would show a depressing literal-mindedness and lack of imagination. “Cyber warfare” is a mugs game.
Russia is a petrostate. The way to hurt them is to drive down the price of oil and gas for a very long time. Alternative fuel subsidy and technology development plus a carbon tax, to drive down demand, and a benevolent attitude towards fracking to drive up supply will give Putin the vigorous screwing he so richly deserves. It will just take a little longer, but it’s a much surer way.
Russia wants to be taken seriously? They want to be the main enemy again? Ok, here’s a coherent foreign policy initiative that forces them to react to us, for a change. I doubt very much that Putin’s position will seem quite as secure in a couple of years, when he can no longer bribe his oligarchy and appease his public using wealth from mineral extraction.
Mary G
w
That brings back some bad old memories {shudders} of my work life. Especially of this guy named Lloyd who could not spell to save his life and
loved to use the “amazing effects” between every.single.slide.
Adam L Silverman
@Smedley Darlington Prunebanks (Formerly Mumphrey, et al.): Ahhh, ok.
SiubhanDuinne
I’m going to assume you’re an Edward Tufte fan.
Helen
Why did HBO just tell me that Girls’ last season is in 2017? I thought that shit was over.
Adam L Silverman
@SiubhanDuinne: I have no idea who that is. That’s what we call briefings with lots of slides with way too much stuff on them.
?BillinGlendaleCA
@redshirt: So you finished building the bunker?
WaterGirl
@Helen: I don’t know the answer to your question, but I did want to raise a glass of wine in honor of your last night (I presume) before you leave.
Timurid
@Mary G:
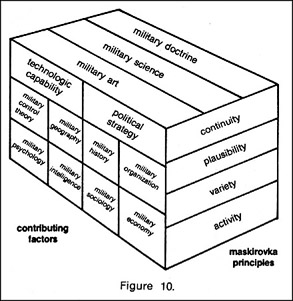
Speaking of Death By PowerPoint… why did Adam leave out the DoD PowerPoint Warrior Time Cube thingy at the top of this post?
redshirt
@?BillinGlendaleCA: I already won this debate. A bunker is not required.
Bill E Pilgrim
Dahling, anybody can take Washington…
Omnes Omnibus
@redshirt: Bullshit.
Adam L Silverman
@Timurid: Oh, the Maskirovka diagram? Oversight. I’ll add it now.
redshirt
@Omnes Omnibus: Sore loser.
GrandJury
@gf120581: I want to see them all fired. Also want to see Obama doing something about it at the highest levels. President Hillary can’t because it will appear vindictive.
Omnes Omnibus
@redshirt: Name a compound other than Compound W that doesn’t have a bunker. You have a camp.
Matt McIrvin
@SiubhanDuinne: I recall hearing that when George Washington was trying to get French-Canadians on his side during the Revolutionary War, he had to order his men not to burn effigies of the Pope on Guy Fawkes Day.
redshirt
@Omnes Omnibus:
You’re wrong, you’ve been proven wrong. Go and look it up.
Bill Arnold
Just saw the Bill Maher interview of B. Obama – very good, worth watching.
Full video here. Note wink at 8:31.
(I recall slightly different wording, looking for a transcript)
Bill Arnold
@Mary G:
Classic visualization (OK, 2009):
“Every time you make a PowerPoint, Edward Tufte kills a kitten”
Omnes Omnibus
@redshirt: I notice you don’t provide a link. Probably because it mentions bunkers.
Bill Arnold
@Adam L Silverman:
You’re looking for “The Cognitive Style of PowerPoint”, Edward Tufte.
Here’s the official link, not full text.
If you search you will find a probably-not-legal link, which should probably not get posted here (so I edited it out).
redshirt
@Omnes Omnibus: Stay in your bunker.
Feel free to provide a definition that backs your claim.
Omnes Omnibus
@redshirt: Those definitions are classified.
Adam L Silverman
@Bill Arnold: ok, thanks
Steeplejack
@redshirt, @?BillinGlendaleCA, @Omnes Omnibus:
Oh, Christ, I am not mediating this twice in one week. You guys knock yourself out. Preferably with bunker-busters.
Steeplejack
CSI: The Cyber folded too soon. Damn you, Jerry Bruckheimer!
I wonder if we can get Patricia Arquette back. I know Van der Beek’s schedule is open.
WaterGirl
@Steeplejack: You can’t be serious, right? That was possibly the worst show I have ever seen. Quit at episode 1.5, I believe.
redshirt
@Steeplejack: Omnes knows he’s lost. He’s just too proud to admit it.
Steeplejack
@WaterGirl:
We seem to be not on the same humor wavelength tonight. I would have thought that CSI: The Cyber was a tip-off.
Adam L Silverman
@Steeplejack: I’m waiting for CSI: The Nuclear!
Ruckus
@WaterGirl:
I’m 1.5 ahead of you. I figured that CSI would be crap no matter which version. I’m quite sure I was 100% correct.
WaterGirl
@Steeplejack: well what i want to know is – has it really been cancelled? Finally?
Mnemosyne
@?BillinGlendaleCA:
To answer your question from, like, two days ago: yes, Buster Keaton’s College was largely shot at USC. It also contains the only known instance where Keaton did not do a stunt himself: when his character pole-vaults into a second-story window to save the girl, he had to hire a USC athlete to do the stunt because he couldn’t figure it out.
It also has the only blackface scene that I’m willing to defend, because (a) he doesn’t resort to stereotyped behavior and (2) when the black characters figure out that he’s a white guy in blackface, they’re pissed.
WaterGirl
@Ruckus: You win. That’s 67 minutes I will never get back.
redshirt
@Adam L Silverman: CSI: CSI
Omnes Omnibus
@redshirt: Poking you on this is fun. Now get to work on that bunker.
redshirt
@Omnes Omnibus: My replies are in jest as well. See? We have a similar sense of humor!
But seriously, I have lead wall in a basement. All set on the bunker front.
Steeplejack
@WaterGirl:
Yes, it was canceled, and, yes, it was awful!
Steeplejack
@Adam L Silverman:
Followed by CSI: Back to the Stone Age.
Adam L Silverman
@Steeplejack: Wasn’t there at least one episode of the Flintstones that involved a police investigation?
WaterGirl
@Steeplejack: First, I could not believe they didn’t cancel after a few episodes. Then I could not believe when it was renewed.
Steeplejack
@Adam L Silverman:
Dunno. My Classic Television Studies major was Perry Mason.
Future Oscar winner Louise Fletcher on right now (MeTV) in “The Case of the Mythical Monkeys” (1960).
Adam L Silverman
@Steeplejack: Enjoy!
NotMax
@Steeplejack
FYI, The Defenders season 1 was released on DVD very recently.
TheMightyTrowel
@Steeplejack: Mitchell and Webb got there first: caveman detective
redshirt
@NotMax: Wha? They just started filming that show!
Groucho48
And, let’s not forget the very short lived Deadwood spin-off– CSI-Deadwood, or, C**kSucker Investigations