As more information is released about the hack on the DNC servers – and I don’t mean the dribbling out of emails with people’s personal identifying information (PII) at Wikileaks – it is becoming much, much clearer that the attacks were broader and deeper than originally estimated. As has been reported, the FBI is investigating the attack as an act of cyber espionage. Specifically, that the hack is a Russian Intelligence cyber operation and US government officials have begun to speculate that it was done to impact the upcoming Presidential election in a manner preferred by the Russian government and Vladimir Putin. This has also been suggested by Clinton campaign officials. CNN has reported this morning that the DNC was warned by US government officials of the weakness of their system during a time period when similar attacks were being made against the White House and other US government systems. Russia seems to be intensifying its attacks against US cyber systems similar to state sponsored active measures used to achieve political effects:
“The release of emails just as the Democratic National Convention is getting underway this week has the hallmarks of a Russian active measures campaign,” David Shedd, a former director of the Defense Intelligence Agency, told The Daily Beast. Shedd said that additional leaks were likely, echoing an opinion expressed by U.S. officials and experts who said that the release of emails on Friday may just be an opening salvo.
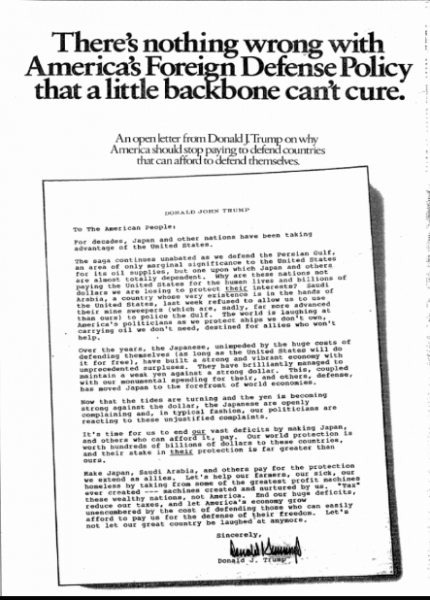
It is important to note that despite the compelling, but circumstantial case that Josh Marshall has laid out at TPM, that Putin’s preference for a Trump Administration may be solely rooted in the simple fact that Trump has long espoused views about American involvement in the global system that overlap with Putin’s understanding of Russia’s interests and his strategy for achieving them. In 1987 Trump spent about a $100,000 to pay for ads in several major newspapers attacking the Reagan Administration for allowing our allies and partners – NATO and non-NATO – for taking advantage of us and not treating us fairly. You can see a copy of the ad below:
Trump’s anti-NATO and anti other alliance position is not something that he just adopted last Fall or because one of his advisors with ties to Russia suggested it. Rather it is a very long standing position of his and I’m not sure anyone knows how he came by it. Given two candidates for President of the United States, one who has expressed a willingness to be somewhat more hawkish than the current President in US-Russian relations and the other who has, for at least 30 years, held the position that the US is being taken advantage of by its NATO allies, as well by its non-NATO allies and partners, it would make sense that Putin would prefer the latter to the former as the next President of the United States. In the most basic terms: Trump has long held views that Putin shares, Putin is smart enough to know this, therefore Putin using his resources to independently try to assist Trump would make perfect sense. Given what we know of both men’s long standing preferences on US involvement with NATO and other alliances there is no need to go looking for dots to connect here on the affinity of one for the other on this issue.
What this leaves us with is a very important concern: what does the US do now to protect the integrity of its electoral system and election infrastructure. Dave Aitel, the CEO of Immunity Inc., in a very thought provoking guest editorial at Ars Technica, makes the argument that the Russian Intel hack on the DNC is very clearly an act of cyber war. And that it raises critical questions about the ability to safeguard the integrity of the upcoming election. Here’s an excerpt, but you should really click across and read the whole thing:
The US government has a decision to make here. If it does not come out strongly against this action by the Russian intelligence services now, then when will it? How is our election system not to be considered “critical infrastructure” that foreign governments are forbidden to interfere with, unless they wish to trigger a serious confrontation with the US? If hacking a presidential campaign and dumping its strategy on the Web is not interference and disruption of a critical institution, then what is? Should we wait until foreign operatives interfere with the primary process? Is the red line only to be drawn around hacking actual voting machines and changing the results?
Bottom line: the US must have an escalatory policy in place for this type of foreign interference. If we do not respond strongly to Russia’s actions in this election cycle, then we risk weakening our country’s deterrence and opening the door to future attacks, which may be even more disruptive to this country’s most fundamental democratic process—that of electing new leaders. Likewise, we should reach an agreement with other nations that we will not interfere with the nuts and bolts of their electoral processes, either. It’s either that, or we need to invest in robust cyber-protections for all presidential candidates at the federal level, stretching our already understaffed Secret Service.
People in the policy area often consider “cyberwar” actions limited to things that causes physical harm or casualties, or things that can replace a 500 pound bomb. But if you cannot manage your people, or protect the American economy, or elect a new President, you have lost a war.
Aitel’s editorial raises the important question: what do we do about this? We know that our electronic voting machines are vulnerable to hacking. Given that we decentralize our elections to the state and local level, we have 50 states and 3,144 counties that use different electoral systems, processes, and machines. This makes US elections highly vulnerable because there isn’t just one system that needs patching or one process that needs to be reviewed in regard to its security protocols be they cyber, personnel, or material. Florida and Utah have already seen cyber attacks on elections, elections processes/systems, or governmental processes/systems in those states.
One of the real concerns going forward, apart from embarrassing email chains with PII being posted on Wikileaks, is not just that Russian Intelligence can get in and look around and take information out of these systems in the US, but what happens if they decide to mess with what’s there? Voter registration information, voter donation information, electoral results, and more are all stored electronically. The next attack may not be interested in embarrassing staffers and causing a few days of reporting about what they wrote. Rather it might seek to remove voters from the rolls or change the reported results of an election in specific locations before they can be reported. And since our system is decentralized, securing all of it is going to be difficult and expensive.
I’m not a cyber expert. I have taught a course on cyber crime and cyber terrorism and supervised graduate research on these issues, but the technical side of this is not my bailiwick. That said the US, as Aitel identifies, has to respond. And here we are back to where I’m familiar: ends, ways, and means. The end state – the objective to be achieved – is deterrence against these attacks. This deterrence must take two different forms. The first is to get the best possible safeguards in place to protect the numerous and varied systems and processes in place at the Federal, state, and county level in the US. The second is to respond to Russia’s cyber attack in such a way that they get the point that they’ve gone to far and any future attempts will be dealt with quickly and harshly, but without causing an escalation of the cyber warfare or, even worse, moving the skirmish from the cyber domain into the actual Land, Sea, and Air domains. Again, I have no idea how this should be done, let alone what is even possible, but the objective has to fall within these two reinforcing dimensions of defensive and offensive deterrence. Ways and means are a bit tougher to estimate as so much of what is done in this arena is just not known even to the vast majority of people with clearances. We all joke about the NSA being unwilling to send us backups of our hard drives and/or complain that they’re probably listening to our calls, but this is what we have the NSA for! And several other agencies and departments of the US government and counterparts at the state level. The subject matter experts and technical specialists in these departments and agencies must be tasked to develop the ways and means to achieve these ends. Even if its just randomly turning the lights on and off wherever Putin is trying to sleep at any given time or making the meow mix theme song play on a repeating loop every time he turns on the TV, radio, or his iPod until he gets the message that the US can reach out and touch him in the cyber domain as well whenever it wants to.
The other thing that has to happen is that the news media needs to stay on top of this as an important, ongoing event to be investigated and reported on within this year’s election. Americans need to be kept fully informed that for once the often used, but seldom accurate, assertion that someone is tampering with a US election is actually true this time. Americans have been primed for decades to worry about voter fraud and vote tampering because of partisan efforts to use the almost non-existent threat of voter fraud, and the news media’s obsession with scandal, for partisan ends. Staying on top of this story, a story that is about electoral manipulation for a foreign power’s advantage, is right in the news media’s sweet spot.
It was interesting to watch Chris Matthews last night make a parallel comparison to the actual Watergate break in. He explained to his panelists that that was a physical break in on the DNC and this was a virtual break in. When Michael Steele correctly indicated that Watergate was really about the corruption of the President/Presidency, Matthews responded that this is about the corruption of electing a President. A lot of journalists, both reporters and commentators, came up during Watergate and view the news media’s reporting as a clear sign of how to do proper journalism. Many who came up after Watergate do as well – almost too much given the chasing of every possible shiny object as a potential scandal to be reported on creating the next Woodward, Bernstein, and Hersch and giving us “gate” affixed to everything. This story seems to be developing legs and the longer the news media stays on it, the better it will actually be for Americans and the upcoming election. It will keep the pressure on to secure our electoral systems and processes. And it could, if handled correctly, lead to long needed reforms to better secure these systems in the future in order to ensure that every eligible voter that wants to vote and does so, has that vote accurately counted and faithfully restored.

Adam L Silverman
I’m going to be offline for the next several hours, but will try to get back into and to comments/questions later this afternoon/evening.
Have fun!
msdc
I support this message.
Villago Delenda Est
How this plays out depends on whether the vermin of the Village think that there are ratings to be had playing up the story.
That’s the sad truth of the matter.
JDM
Really doing something to stop this sort of thing requires – as one element – we stop forcing companies to include back doors in their software. So if (more likely “since”) we aren’t going to do that, we are starting out by crippling our chances.
Matt McIrvin
It’s a natural consequence of Trump’s general attitude toward money and the “Art of the Deal”, isn’t it? To wit, if you’re not screwing your partners over for as much as you can, you’re the sucker. He believes the United States should be run like a business that is run by Donald Trump: a deadbeat business.
CONGRATULATIONS!
Well, I’ve been doing this “cybersecurity” (or whatever you want to call it) thing for almost 15 years now. I can tell you this: citizens don’t take it seriously. Corporations fight it tooth and nail. The government says they take it seriously, but don’t. If they did, most defense contractor CEOs and their IT people would be in prison and we’d be recruiting the best hackers for seven-figure jobs working for the armed forces. Like Russia and China do. The adversaries (Russia and China, mainly, plus a bunch of supposed “friendlies”) take it very seriously indeed.
I can tell you how this ends: one day, everyone in the US wakes up, goes to the ATM, and sees “balance: $0.00”. Then and only then are Americans and their government going to take it seriously, but by then it will be far too late.
Fair Economist
I didn’t think about hacking electronic voting. That’s really scary.
Hunter Gathers
We have Russia trying to tilt the scales in order to elect an ignoramus who will allow Russia to re-take the Baltic States with a minimum amount of effort while said ignoramus tries to turn NATO into a protection racket. But we must respect the ignoramus, because he salves the hurt fee-fee’s of racists and morons.
Cermet
This is win/win for the Gop – they can scream that without major voter ID laws our election results can be tampered with AND they get help from Putin for his sock puppet tRump. (Putin needs to really clean his arm and hand considering considering how far that asshole has his arm up tRumps rump!)
Cacti
I had no idea until recently how dependent Trump’s businesses concerns were on Russian money.
No major US bank will finance any Trump projects because they’ve all been burned by him.
Betty Cracker
Great post, Adam! This, though:
What kind of monster are you? LMAO!
Seriously, I have noticed the Russia angle gaining legs in the MSM, and I’m glad to see it.
Anoniminous
We learned back in the BBS days the only secure computer is one that completely blocks program and program storage memory from the outside. Windows, Linux, and O/S X are insecure by design and it takes an inordinate effort at a significant cost to secure them and even then only maybe.
Villago Delenda Est
@Cacti: They have lots of experience with the deadbeat.
No mas.
singfoom
@CONGRATULATIONS!: From my perch in the tech industry, this is accurate. While some teams within a given corporation care DEEPLY about security, for most it is an afterthought. I don’t know anything about defense contractors though, so I’ll take CONGRATULATIONS words for it.
The only solution for this specific instance I can think of is for the FEC to rule that party hardware/software infrastructure needs the equivalent of a PII audit. But even then, you’ll have people gripe about the implementation because real security in depth is hard and inconvenient.
West of the Rockies (been a while)
I kinda thought the post referred to our local troll patch that has cropped up lately.
As for The Bear in the Woods… I imagine our cyber dudes are returning fire, as it were.
Anoniminous
@CONGRATULATIONS!:
This. A thousand times this.
mudslide567
@CONGRATULATIONS!: THIS!!
Pogonip
@msdc: I think the Geneva Convention prohibits Meow Mix attacks.
Hunter Gathers
@singfoom:
Christ, I can’t even set a password policy at work because a bunch of Trump voters will get pissed off. So the network that I administer is as secure as as a wad of dollar bills at the ‘gentleman’s club’. Yay me!
sigaba
@Cacti:
Yeah, for someone who’s so uptight about corruption and money in politics…
Pogonip
@CONGRATULATIONS!: and that’s when I start trading toilet paper and cigarettes for–well, pretty much whatever I want. :D
Miss Bianca
Meo Mix theme song? Oh, Adam – of course you realize…this means war..
On a more serious note…my tech guru and I have been cleaning out nests of Russian and Chinese hackers trying to brute-force their way into my little website (mostly by “black-boxing” their IPs, but that’s a band-aid at best). I can’t even imagine the levels of attacks aimed at our more critical infrastructure.
gvg
If he is trying to influence the election….why do it in a way that gets noticed and reflects badly in his preferred candidate? I am guessing Russia hacked the white house because of course they did if they can and the DNC because Hillary was a likely candidate. what about the other candidates? they couldn’t all have moles on staff….when I was a kid i think all presidential candidates gave some thought to not having anyone with ties like Trump or Sanders on staff……now it looks like we are complacent and don’t think of these scenarios ahead of time.
Do the Russians think they aren’t noticable when they hack?
slag
The only question on my mind after this Russian attack will be whether John McCain bursts out and exclaims, “We’re all Democrats now!”.
Pogonip
@Hunter Gathers: ??? What do Trump voters have to do w/your company’s passwords?
Alao, I have Quilted Northern on special today.
Mike in DC
I guess an 8 warhead Trident D-5 detonated in the exo atmosphere above Moscow, triggering an EMP covering half of Russia is off the table? Bummer.
Hack their stuff and release something linking Putin to the assassination of every dissident over the last dozen years. Then email it to every address in Eurasia.
Emma
@Cermet: No. This has nothing to do with voter ID and in this situation it would be slapped down.
singfoom
If anyone is interested, you can watch a virtual map of real time attacks at this site by Norse:
Norse Attack Map
Pew pew pew…mostly coming into the US
? Martin
I don’t think Trump is directly connected with any of this, but I think he’s in a difficult situation where he is more beholden to Russian finance than he would admit (or that his tax returns might reveal) and that gives him a natural predisposition toward Russian benefits. That is, for a guy that cares only about making deals, Russia is willing to deal where other nations (including the US) are not. Because he believes in his power to close deals favorably, he does not worry about Russia – they are playing his game after all. But I honestly don’t think he’s able to differentiate between himself and the nation. That is to say, I think Trump may be the ideal target for a spy agency – someone who can’t morally differentiate between his personal gain and the non-personal assets he gives up. To him it’s just a good deal, and we gave him the assets by virtue of electing him to office. The email hack is just another way of proving to Trump that Russia is willing to deal.
What’s most discouraging is that if any of these things were true about Clinton – campaign manager who worked for Russians, taking funding from them, any sort of hesitation on NATO – it’d be the end of her. The media would explode in outrage. It’s just all waved off with Trump, as when your 3 year old says they hate you, and you know it’s simply because they have no better words to explain why they are unhappy.
FEMA Camp Counselor
@Matt McIrvin:
Yup. Trump views the world as basically a series of zero-sum games where if you’re not winning and dominating, your being screwed.
This also explains why bigots love the guy. They view rights as a zero-sum game were if one group is gaining, the other must be losing. Trump appeals to that part of their lizard brains.
hovercraft
I just posted this in the other thread.
RNC Brings Omarosa To Philly To Respond To Clinton On Foreign Policy via TPM
This campaign has become a complete farce, what’s next Gary Busey health care tzar? Check out the twitter mockery at the link.
MattF
OT. How hot is it in Saudi Arabia these days? This hot.
Miss Bianca
@efgoldman: OMG…Meow Mix is bad enough, but “It’s a Small World” counts as genuine torture.
singfoom
@efgoldman:
I’ll give you that government agencies will be relatively secure, but the idea that our political parties are secure is just wishful thinking. Otherwise this whole DNC e-mail thing wouldn’t have happened.
Even relatively secure systems can be hacked with a combination of spearfishing and social engineering. I don’t know the details of how the DNC hack happened at the moment though.
? Martin
@efgoldman: For all we know the DNC does have that level of security. But there’s a difference between hiring a security outfit to protect a bank (even a gigundo one) from robbers and hiring the US Army from protecting a nuclear stockpile from a foreign state.
When you have Russia or China state-sponsored attacks coming at you, rent-an-infosec is unlikely to be up to the task. It’s why we give Secret Service details to candidates – they have foreign intel access that a private security cannot have. It might be time for the same to happen for digital – giving candidates an anti-cyber team that operates in conjunction with the State Department or other appropriate agency.
Ella in New Mexico
@CONGRATULATIONS!:
So what you’re saying is that the Russian government and Putin are the alt-universe, mirror image “Mr. Robot”?
TaMara (HFG)
@Adam L Silverman: Great. Now I’m going to have nightmares for the next four months. Thanks,
ObamaSilverman.Barb2
Adam – Thank you for your work on keeping us informed about cyber attacks!
Technocrat
@singfoom:
And the “realer” the security, the harder and more inconvenient. Lazily stated, if the average American corporation became actively security-conscious their business would probably grind to a halt.
Defending against cyberattack is like defending against an invisible sniper – you have to be completely vigilant all the time, even when they’re not stalking you.
dr. bloor
@Villago Delenda Est:
Maybe they can figure out a way to do a tie-in with Damon’s new Bourne movie.
John Revolta
@efgoldman: Read Josh Marshall’s article at TPM (link upstairs.) Scary stuff.
Stan
@Cermet: I rather thnk this is lose/lose for the GOP. I don’t think the public will take kindly at all to Russian interference in US elections, if they come to believe that is what is going on. Not at all.
Second, it’s unfortunately true that the GOP has successfully branded themselves as the party of strong defense in recent decades. This alliance of Trump and the Russians against the US will put some hurt on that brand.
Miss Bianca
@TaMara (HFG): IKR? I saw a comment this morning from one of the threads last night where he had started to outline this stuff and I was all, “damn, I’m sure glad I didn’t see this before I went to bed!”
Hunter Gathers
@Pogonip: They don’t want even a minimum character # policy. And the ones who won’t let me (including the owner) are all Trump enthusiasts. So I be screwed.
Miss Bianca
@? Martin:
Yeah, if they havent already, I’d say this would be an excellent plan!
CONGRATULATIONS!
@Mike in DC: Effectiveness vastly overrated by bad writers. You end up killing a lot of the power grid transformers temporarily, but the IT infrastructure you’re trying to hit will emerge largely unscathed. Not to mention that to those on the receiving end, it’s going to look like a nuclear exchange and not a disabling one-off. With predictably catastrophic results.
? Martin
A bit of a thought experiment. US banks won’t lend to Trump because they see it as unacceptably risky. Their recourse for non-payment is to sue, and they probably expect that Trump would tie them up so badly they’d only recover a fraction of their money (or that he’d just use bankruptcy laws to avoid payment).
So if Russians are willing to lend to him, they have the desire to be repaid as the US banks. What mechanism to do they use to recover their money? I suspect it’s not US civil law. Seriously, what’s their collateral and preferred recourse?
Villago Delenda Est
“We are at Cyber War! So what, exactly, do we do about it?”
Release the Pokemons!
Villago Delenda Est
@? Martin: “It would be a shame, Mr. Trump, if anything happened to your daughter.”
Matt McIrvin
@CONGRATULATIONS!:
And by doomsday preppers.
blackcatsrule
Can the powers that be please create a Quick Link for the Adam Silverman posts like we have for Richard Mayhew, recipes, etc? They are so informative especially in this election season. Thanks!
Mike J
I think most of our people would argue for exactly the opposite.The last thing we want is for our peer competitors to know where we can get. Let them feel safe. Iran had completely air gapped their nuke program and we still destroyed millions of dollars worth of centrifuges. In cyber, if you let the other side know your capabilities, you lose that capability.
D58826
Expensive is the magic word. If Congress can not pass a 2 billion dollar appropriation to fight Zika or the level of arm twisting that was required to get Sandy relief money passed or the effort required to get them to fund medical care for 9/11 first responders then no way are they going to fund this. The only money they might come up with is it looks like they can use it to embarrass the democrats.
singfoom
@Hunter Gathers: Not even a minimum password policy? Holy shit that’s bad. I’m sorry that you have to deal with that. Introduce them all to lastpass. That’s what I keep doing with my not so security conscious relatives and friends. Sure, it’s cloud based, KeepassX would be more secure by being local, but it’s an improvement.
Mark
I had the good fortune to see Alex Gibney’s “Zero Days” recently and it deals with these questions exactly — in the context of Stuxnet. One thing I didn’t realize is that the NSA doesn’t have legal authority for offensive cyber operations against other countries — but another agency does, and it is housed at the NSA and has the NSA director as its head.
It’s a good example of the kind of weird BS that had flourished under the cloak of extreme secrecy, which will increasingly hamper us in arriving at sound policy in the arena of cyber warfare. I highly recommend the film.
Origuy
@singfoom: I work near the Cyber Defense Group offices at my company; they have this display and several others on the wall outside their offices. Scary.
patrick II
I used to work at a large Dept of Army software house. I knew people, and one person in particular, who could break into any computer system regardless of security measures. Because of that, I do not like electronic voting machines, particularly those with no paper backup. (My voting district is moving away from those in the next election. But even with paper backup, most states only do a recount if elections are very close, so most of the time paper ballots are never counted.
In 2004 the Ohio voting machines were electronic with no paper backup, networked to the private corporation who made the machines, headed by a Bush supporter, where the votes were electronically “tabulated”. In Ohio that year the exit polls showed a larger Kerry vote than the electronically tabulated vote count. I don’t want to sound too crazy and say that election was stolen, but, because there is no real paper trail, no one can prove it wasn’t.
JPL
Adam, Please consider writing an opinion piece for the Washington Post or NYTimes. Maybe Congrats at comment 6 can assist you.
Suffragete City elftx
I know several people on facebook who are hoooge Trump fans. They also spend a lot of time decrying any flag desecration..all while wearing their flag hats, and boxer shorts, etc. I will be finding out if they think what is in those emails is more important than the fact security analysts are pointing directly to state espionage and if so they can shove that flag where the sun don’t shine.
Villago Delenda Est
@patrick II: The stink of the Ohio situation was such that Diebold (who provided the machines and the CEO) got out of the electronic voting business because their banking business was called into question about its integrity.
It is so typical of this fucked up country that the security required for ATMs is more seriously fretted about than the security for elections.
CONGRATULATIONS!
@Hunter Gathers: “Password1234. There’s your minimum characters. Happy now, asshole?”
-Actual user email I’ve gotten. Before I got promoted to the point where I could cause those kinds of users grief.
? Martin
@Miss Bianca: Campaigns will be a nightmare to secure however, because they are so dependent not just on volunteer staff, but also on short-term staff. There are few organizations that deal in rapid build-up/tear-down of staff on the scale that campaigns do – and that extends into the transition team period. They are HR nightmares and as a result they will be extremely difficult to secure well without becoming cripplingly bureaucratic. Moving to physical interfaces for electronic security would help immensely – TouchID on an iPhone, for example as a *requirement* for access. Those types of things really make it a lot more challenging to attack remotely.
cmorenc
The RNC itself may be in for ugly surprises about cyber-intrusion. If Russian hackers sponsored by their intelligence services have been attempting (in some cases successfully) to invade US government agencies and the DNC, then it’s near-certain that they have also made similarly serious, determined efforts to hack into the RNC as well, irrespective of the extent the attempts have so far been detected. OK, so paranoia about Trump campaign manager Paul Manafort’s lobbyist ties to Russian-backed Ukranians might even suggest that the Trump campaign are quietly “in” with the Russians on monkey-wrenching the DNC, but I seriously doubt any such covert cooperation, if such exists, has bought the RNC any immunity from similar Russian cyberintrusion. Putin will happily monkey-wrench the Republicans the moment he thinks it’s in his and Russia’s interests to do so.
JPL
@CONGRATULATIONS!: How many election machines in each precinct would have to be verified with paper ballots, to insure a clean election.? Maybe equip one machine with a printer, if possible.
piratedan
well, whatever you do, don’t read the comments at ARS, those fuckers don’t believe in anything other than their own technical prowess and after reading a couple of pages worth of comments, I can see how we ended up with Ed Snowden. All of these folks believe that their special set of skills places them above such trivial matters as being beholden to any side or that there is any difference between any side. Truly fucking scary.
JPL
@cmorenc: That’s when the blackmail starts.
Matt McIrvin
@cmorenc: But that moment is probably after his guy is safely in the White House.
Villago Delenda Est
@piratedan: Arrogant nerds are arrogant nerds. Film at 11.
Matt McIrvin
@piratedan: Pretty sure some of them believe in truly odious and cuckoo-bananas alt-right crap. Mencius Moldbug kinda stuff.
? Martin
Quite the collection.
Smedley Darlington Prunebanks (Formerly Mumphrey, et al.)
Well, one of the frustrations about this is that, even if we do something to fuck with Putin and put a little fear into him, my guess is that they’ll have to keep it secret, and we’re unlikely to ever know about it. So we get to worry, even if things are getting better. I hope I’m wrong about this, since I know less about cybersecurity than I do about subatomic particles, and I don’t know anything about subatomic particles…
germy
@Miss Bianca:
Why not the USA Freedom Kids* on endless loop?
.
* I just learned their manager is suing Trump for breach of contract!
Miss Bianca
@? Martin: I’ll look into that – not because I’ll be providing Internet security to elections, but because the whole issue of Internet security is so damn important I want to learn more about it.
Jewish Steel
Excellent summary of events and their implications, Adam. Thank you.
lumpkin
How’s about we just have properly constructed paper ballots and a sufficient number of people to count them and simple oversight systems to prevent cheating. Way cheaper and more robust than any level of cyber security.
West of the Rockies (been a while)
@hovercraft:
Huh… I guess they couldn’t afford the guy who played Redshirt #2 in The Gamesters of Triskellon.
Technocrat
@piratedan:
Wooo, I should have heeded your warning. That was horrifying.
CONGRATULATIONS!
@JPL: That’s not a question that can be answered. For starters, if the machine is compromised so too will be the printer output.
Second, what’s your goal? Harm reduction or elimination? I’d go random samples if “reduction” is the goal, “paper ballots and pencil” if elimination is the goal. For what little my opinion is worth I see absolutely no reason that we shouldn’t be on “paper ballots and pencil” nationally. There’s many time-honored ways of messing with that count as well, but the good news is that we know what most of them are, and where those threats come from.
? Martin
@Villago Delenda Est: Yeah, that sounds about right. I wonder if we found out where BiP works.
Mnemosyne
Here in Los Angeles County, we for the most part are still using Inkavote (aka Scantron) ballots, though they keep rumbling about switching to all-electronic.
There is apparently some fuckery that can be done with the scanning software if someone is motivated, but there is also a piece of paper that can be evaluated and read if necessary.
CONGRATULATIONS!
@Mnemosyne: Where you run into the security meatgrinder with the Inkavote systems – indeed with all electronic voting – is not the individual machines (although they wrongly get all the attention) but the machines that count and aggregate those results. Those are just as hackable and give a lot more “bang for the buck” if one were to do so.
Mnemosyne
@CONGRATULATIONS!:
Right, but the Inkavote ballot is constructed in such a way that it would be simple to hand count instead of machine count. It would take extra time, but there’s no “hanging chad” to worry about.
EZSmirkzz
Well Adam, first things first. Security is a myth. Even if we had perfectly secure machines, which we cannot be assured of because all of the low level code is closed sourced, so chipping is a real possibility. That’s why China and Russia are developing their own chip industries, because they don’t trust American companies that manufacture overseas not to back-door the hardware. Add the greed, and the disloyalty of of some of the employees of these companies that have access and capabilities to back-door the software, along with general coding errors that leave zero days for exploitation by state actors, and then proceed to boot your machine.
Let’s assume the loyalty and good pay of all the employees and developers of operating systems, so that there is absolutely no chance of intelligent agency penetrations, or coders gone bad, and look at the sheer complexity of what wish our machines to do. MS-DOS used to boot up on a single 5 1/4 floppy. Same as the US strategic nuclear forces still use. Now the typical OS won’t even fit on a CD weighing in at 720 megs.
From the ground up, insecurity is built in. Your fifty state and 3,144 counties are small potatoes in the schema. Even if all of these millions of machines were upgraded, and configured correctly, which they are not, you still would have the underlying code chock full of zero days.
Add in commercial software for watching cats, porn, and twittering on facebooks and the attendant billions that haven’t got a clue about passwords, (apparently 123456qwerty passwords are still the rigor,) reused on multiple sites, (thank you John for maintaining anonymous cowards commenting!,) and we can move on to attribution of attacks, once we eliminate ISP and carriers selling information about their customers, up to and including mirroring users surfing, and their millions of well paid with less than than living wages, and always loyal, unlike the loser lone wolfs with .233 tumblers killing for God and country.
It is nearly impossible to attribute a skilled attackers location because the internet was designed on a trust model, and that model is easily spoofed by not only the skilled, but rookies as well. (You can call them script kiddies is you’re into disparaging for the sake of disparaging, yet I digress.) You can rent networks, you can spoof IPs, you can masquerade OSes, it just goes on and on.
PL thinks it’s GRU, but capability is not proof of culpability, so any retaliation would have to follow the same non-attributable path ways as the original hack of the DNC, which may or may not have had their systems as hardened as they could be humanely made, ( I have my doubts, YMMV). I would say blame WikiLeaks because shooting the messenger is the American way, but that wouldn’t resolve the dilemma of overly complex systems doing extremely complex task initiated by loose nuts on keyboards, and keypads.
If we are to say that this crack of the DNC is an act of war, then retaliation is also an act of war, and at this level, not exactly where you want people getting their flags crossed up. Nor is the crack worth the revealing of American capabilities.
We have to ask ourselves if our own interference in other nations internal affairs is really that much different than this, or if it is just par for the course of international relations, just by another method. We may not like Russia or China or half a dozen other countries interfering in our Presidential election, but it hardly holds us back from doing the same thing. Given our activities in Russia’s near abroad, this may be their way of turning America’s lights on and off, and playing Hail to the Chief every time we turn on the television.
BR
@Mnemosyne:
The reason for that is because of Sec. of State Debra Bowen’s voting machine analysis, which was unprecedented. She hired real security experts and they broke the machines in ten different ways. Then she told the voting machine companies that they had to fix them or be decertified, and of course they couldn’t fix them, so she pushed the state back to optical scan paper ballots plus a manual recount in close races.
The thing that’s great about paper ballots is that they are basically unhackable, scale up really well (no long lines because all you need is a pen), and can be supplemented by touchscreens that print ballots for those who have poor vision.
Shana
@hovercraft: The other thing the brain trust at the Trump campaign did yesterday was hold their big rally in Roanoke VA (in a hotel ballroom where he complained about how hot it was, during a 100 degree day) while 1,000 people (among them my older daughter) descend on the town prior to taking the bar today and tomorrow. A fair amount of gridlock ensued I believe.
Of all the towns to pick, they pick the one holding the bar exam.
? Martin
I think the concerns about voting machine hacking are a bit overblown and miss some of the potential benefits of electronic voting. For starters, you aren’t going to seek to overturn a national election hacking individual machines. There are far more effective and more difficult to detect methods of doing that.
But electronic voting allows my precinct to offer ballots in over a dozen languages and they never, ever run out of ballots. And expanding the system would allow people that have difficulty getting to polling places to vote. It would necessitate dealing with the voter ID system in a way that would likely be fair to all. What it risks in fraud it could more than make up for in access and turnout.
? Martin
@BR:
That’s not correct. We still use electronic machines in OC.
catclub
@gvg:
Well, the one set of Russians hacking the DNC did not notice the other set, so there you are.
I will believe it was not Russians when the RNC hacked stuff comes out.
gus
I find that ad shocking. Not that Trump held that position, but that he’d given it any thought at all. I just assumed his “pay or we pull out” stance was something he came up with off the cuff.
catclub
@lumpkin:
Too sensible. That is how the Canadians do it.
eldorado
fwiw – i follow a bunch of infosec people on twitter (although i barely understand most of it) and it’s been a solid consensus that this was russian in nature since this started coming out.
D58826
OT but MSNBC just interviewed two Fla. Bernie or bust 40 something sisters. The younger is voting for Hillary because she doesn’t want to repeat the mistake she made in 2000 when she voted for Nader. The older sister is going to vote for the Green party because she wants to punish to corrupt DNC with the voter fraud, stealing the election, failure to challenge Bush v Gore decision in 2000. The reporter asked her point blank if punishing the DNC is more important than defeating Trump and can she live with a Trump presidency. And she said that she had no problem with a president Trump. Punishing the DNC was more important.
What is the matter with these people?
Tokyokie
@srv: Hey asshole, Stevie Ray Vaughan called from the great beyond and wants his initials back.
BR
@? Martin:
With a paper trail, right? I think she allowed counties to opt out of optical scan if the machines produced a printed paper trail.
Smedley Darlington Prunebanks (Formerly Mumphrey, et al.)
@srv: Are you going to unlink 538 from you name when Clinton pulls back ahead?
? Martin
@BR: Yes, with a paper trail. You see the paper before final submission.
germy shoemangler
R.I.P. Miss Cleo
germy shoemangler
@srv: I suspect your life and circumstances will be unaffected no matter who wins the presidency.
That’s why it’s a joke to you.
JPL
This post ties my stomach in knots, especially with the additional comments by those who study computer security and cyber warfare.
peach flavored shampoo
So I see that Trump’s comment about leaving NATO just to run a protection racket got zero play on the MSM today. Threatening to back out of a major, historic post-WWII treaty meant to ensure the relative peace of the world and crickets. Unreal.
CONGRATULATIONS!
@D58826: Malignant narcissism. Of which I suspect that group of horrible people making us all suffer with their disorder is going to rapidly get larger and not smaller.
Villago Delenda Est
@srv: Really is too bad that the circumstances (Drumpf up to his eyeballs in hock to Vlad’s oligarch buddies) lend much more plausibility to this than every “ZOMG Hillary’s classified email!” ever did, now isn’t it?
FlipYrWhig
@D58826: I think they know what the answer is _supposed_ to be and what doing the right thing is _supposed_ to look like, but they want to be in-your-face at every moment leading up to standing before the actual ballot.
Quinerly
@D58826:
I had it on in the background. It’s par for the course. I have yet to see MSNBC interview any just regular old run of the mill Hillary supporters. Just a regular committed supporter from day one. My other bitch about this is how many BS supporters talk about voter fraud and voter suppression unchallenged. There’s a great piece up on Washington Monthly…how the BS supporters have been duped/used.
Villago Delenda Est
@germy shoemangler: “The meeting of the Miss Cleo appreciation society this coming Friday has been cancelled due to unforeseen circumstances.”
BR
@Quinerly:
As I wrote last night — if you don’t like their coverage, please do tell them. That’s the only way they’ll change.
Quinerly
@FlipYrWhig:
I hate to sound snarky. These were grown up women from Florida. The one voting Stein and talking about the DNC and HRC’s voter fraud said she had been a Dem for 40 years. We aren’t talking 20 year BS supporter that got his head tattooed on her breast and is a delegate but didn’t know when the roll call was.
Major Major Major Major
@efgoldman: using paper ballots with an optical count is i believe the gold standard for UN election observers. I’m continually amazed that we don’t have that everywhere here.
Mnemosyne
@srv:
No, no, the message of the day is, It doesn’t matter who provided the emails because they’re all true! Didn’t you get the memo this morning.
It’s all a conspiracy theory was supposed to be embargoed until tomorrow.
Quinerly
@BR:
And I have.?
Iowa Old Lady
@efgoldman: That’s what we use in Iowa too.
Gin & Tonic
@germy shoemangler: Did she see this coming?
Quinerly
@Shana:
Trump has threatened not to pay the hotel. Hotel has responded.
Tilda Swinton's Bald Cap
@Anoniminous: Exactly. Commodity computing with crap hardware and Unix variant OS’s are the main reason. They are incapable of being secured because of their architecture. The only OS that has never been hacked is IBM z/OS (used to be MVS).
? Martin
@efgoldman: I would note that you are far more likely to have vote tampering when those ballots get put in the back of someones car than in an electronic scenario. I can recall a number of situations where entire precinct ballots vanished for days on end because they never made it to the registrar. That’s why Canada does hand counts on site in public. The ballots never leave. They never go into a back room. The count can be witnessed.
Consider that rigging elections is done statistically, like gerrymandering. If the precincts from the most liberal districts ‘accidentally’ get picked up by the wrong person and dumped in the swamp, that has the same effect as actually stuffing a ballot box or faking a ton of voter ids or hacking a bunch of voting machines – but it’s way the fuck easier to pull off and get away with.
When the simplest crimes aren’t being committed, don’t worry too much about the more elaborate ones that would yield the same result.
bupalos
@singfoom: I worked for a translation company for over a decade, with a major atlanta based defense contractor as a primary client. I can tell you they cared about it exactly as much as it was dictated that they had to care about it, and no more. I think it’s probably true that most defense contractors don’t really have competition per se, so in my anecdotal experience they weren’t even as careful with their trade information as our regular customers, for instance those making construction, mining, or computer equipment.
They advised us on how to make our transactions meet formal requirements and appear secure. That is where the concern seemed to begin and end.
Quinerly
@Mnemosyne:
The message of the last two days is if it hurts HRC it’s ok. Doesn’t matter if the Russians did it. I had someone tell me on line that it was funny to him that the Russians are more honest than the DNC and HRC. He cheered the hack. Older male. Bernie supporter by the way.
germy shoemangler
@Gin & Tonic:
Yes. She fought colon cancer for quite some time, but lost when it eventually spread to her lungs.
PhoenixRising
So when the leaks that undercut Trump are released, can we assume that is the Chinese?
I’m thinking Adam has nailed the critical aspect: No need to look for a more specific quid pro quo as Josh Marshall seems to be (it’s likely to be a fruitful search but so what). Trump has long been advocating for the current interests of what is now Russia, and he is borrowing from Russian lenders, and this attack was carried out by Russians, and the leak redounds to Trump’s electoral benefit. All of that is interesting and further rebuts the assertion that Trump is either a successful businessman OR has US interests in mind when reaching for the levers of power.
But what’s more important is, How is our election infrastructure secured against hacks like this one? Assuming that the voters stupid enough to think they should not vote for HRC because the hack embodies their conspiracy fears about the DNC do not form an electoral wedge that matters in the polls by mid-October…will they try, try again to more directly control the outcome?
Is it safe to assume that this didn’t happen 12, 8 or 4 years ago because there has not been a candidate whose selection (aparently) by US voters would be so favorable to Russia’s interests?
germy shoemangler
@Major Major Major Major:
Hillary should put that on her To Do list (if she hasn’t already).
Gin & Tonic
@germy shoemangler: Can you tell me whether that sound you heard was my attempt at humor whizzing over your head, or clumsily clattering to the floor?
Keith P.
Where is Anonymous in all of this? I would have figured they’d have hacked the shit out of Trump by now, since he’s right up their alley. Now that I think about it, I do recall them saying they hacked Trump Organization…maybe they’re waiting until the debates to release theirs? But as a private org, I bet there’s some good stuff waiting for Anon.
Leto
@CONGRATULATIONS!: There’s a reason China’s newest fighter looks a lot like ours (even if it’s not nearly as capable): China Hacked F-22, F-35
Stealth Jet Secrets
We can all laugh at the 35 program being a boondoggle, but that’s R/D that’s a generation ahead of the Chinese and Russians that they’ve essentially gotten for free.
gogol's wife
I just randomly googled “Trump” in Cyrillic and found a blog post on something called “Meduza.” It reviewed the suspicions expressed by the “means of mass information” in the U.S. and dismissed all of them. It did not mention Trump’s indebtedness to Russian interests, and it claimed that there was no confirmation of any involvement of Russian spetssluzhba (intelligence services) in the hacking. I was just wondering how they were playing it. The general tone was one of wry amusement at the wild imaginings of the Clinton campaign.
Poopyman
With all the campaign news today, what’s at the top of the WaPo website? A video titled
To be fair, there are articles about the convention, most recent being this bit of news:
Go Babs!
patroclus
To me, this whole thing shows how media has changed since 1972. When the Watergate break-in happened, imagine if the media had blamed it all on the Democrats, and brought so much pressure on them that they had to fire Larry O’Brien and they just talked and talked and talked about how it would hurt McGovern and how it just re-inforced public perceptions about his dishonesty. And then, like many of the above comments, even Democrats speculated as to why the security at the Dem headquarters was so lax and how embarrassing it was for them. If that had been the reaction then, there would have no special prosecutor, no congressional investigations, no impeachment hearings, Nixon would have continued to reign, the Republicans would have easily won the 1974 mid-terms and the 1976 general election. If you want to know why the Village is wired for Republicans today, look no further than this incident.
RSP
@germy shoemangler:
srv’s callousness about the election and its potential consequences for minorities and other less powerful groups has always struck me as monstrous. You hit the nail on the head; it is all a joke to him because it would not hurt him in the least if Adolf Trumpler gets elected.
germy
@patroclus: Oh, I don’t know. If the RNC had been hacked by Russians, and it was revealed that Hillary was good friends (or at least spoke highly of) Putin, don’t you think the media would be all over it, 24/7?
Would she eventually have to drop out of the race, between the congressional hearings and the non-stop media outcry?
AnotherBruce
@germy:I nominate the “Cars for Kids” commercial.
germy
@AnotherBruce: I just looked at that commercial. It’s certainly annoying, but it lacks the evil of a bunch of kids chanting support for a fraud. And how sad their manager got burned by him. :)
EDIT: wouldn’t it be funny if THIS is what it took to end his campaign? Not the drumpf university revelations, not the racist comments, not the basic lack of knowledge of the issues… but the fact that he cheated the USA Freedom Kidz???!
Quinerly
@germy:
Yes. And Yes.
Mary G
@Miss Bianca: I agree! I haven’t been to Disneyland in years, but I still remember wanting to jump out of the boat two countries in.
Adam L Silverman
@Betty Cracker: Don’t click on that link. Its 10 hours of it on a loop!
Adam L Silverman
@CONGRATULATIONS!: No argument here. Aux ATMs citoyennes!
Trollhattan
@? Martin:
In Sac County we went from chadilicious punchcards to optical scan and have kept those ever since.
Quinerly
Jill Stein in the convention hall being interviewed about how the DNC and HRC “sabotaged” Bernie.
Adam L Silverman
@TaMara (HFG): de nada. Consider it a house warming gift.
Mnemosyne
@Miss Bianca:
@Mary G:
I am one of the few people who doesn’t mind “it’s a small world.” I loved it as a kid and made my mom ride it, like, three times in a row.
I even got to tell songwriter Richard Sherman that I didn’t care what anyone else thinks, I still love it, and he seemed to appreciate that. So there. ?
ETA: Oh, and G permanently won the Best Husband Ever award by going on the holiday version with me, though that mostly had Christmas carols and only one or two renditions of That Song.
Miss Bianca
@Mnemosyne: Haters gotta hate, baby. ; )
jenn
Well, this is a nice optimistic thought! But your post has inspired me to go talk to my elected officials, so thanks.
On the domestic ratfucking front, I just heard that Bernie is renouncing his registration in the Democratic party, and is going back to being an Independent. I was pretty much expecting it, but was hoping that I was going to be wrong – that his using the Dems to prop his own ambition wasn’t going to be THAT obvious. Ha. What an asshat.
Adam L Silverman
@Matt McIrvin: And Speaker Gingrich.
Adam L Silverman
@blackcatsrule: email Alain and cc Cole if you want it to happen. Their contact info should be on the drop down list of contacts towards the right of the page.
And thanks – I’m flattered.
Adam L Silverman
@Mike J: I was being facetious. It would be amusing though!
Adam L Silverman
@JPL: Okay. I have no contacts at any of those places so no way to place a piece with them. Most of my journalistic contacts are correspondents that cover wars.
Quinerly
Reply button screwed up. I have no idea how Stein got in the hall. She has been holding rallies all day outside. MSNBC refused to cover Harkins’ speech about the ADA. Had her in that box overlooking the floor. She got to say “sabotage” twice and that some polls are giving her 50% of BS supporters.
Adam L Silverman
@germy: Shocked, I’m shocked that they have to sue for breach of contract.
The gaudier the crook, the cheaper the patter.
Sam
We could start by making a public attribution with enough evidence to be convincing, both of the original hack and the transfer to wikileaks. Our public security firms are very good at this, turn them loose. Make it a public contest to ID the hackers and the route to wikileaks.
EZSmirkzz
Josh has another good post up on this at TPM. Occam’s razor.
JSYK
Quinerly
Rep Gabbard giving her nominating speech for Bernie now.
japa21
@jenn: Source for the Bernie info please?
jl
@jenn:
” I just heard that Bernie is renouncing his registration in the Democratic party, and is going back to being an Independent. ”
You need to be wary of BS. Vermont does not have partisan voter registration, Sanders cannot register as anything. It is like Illinois, where Obama cannot register as a Democrat. Assuming the person spreading this nonsense is not a troll, maybe they are confused. Sanders has announced that he is keeping his Independent status as Senator from Vermont until his next election campaign, when he plans to run on the Democratic ticket.
Below you can see a complete list of states that have partisan voter registration, with the totals by party. Note that Illinois and Vermont do not appear on the list.
HUFFPOLLSTER: A State-By-State Guide To Party Registration
http://www.huffingtonpost.com/2014/05/27/state-party-registration_n_5399977.html
catclub
@germy shoemangler: I suspect that to-do list is pretty long.
Also many items require some sort of control of the legislature.
Phylllis
@Anoniminous: We were advised to conduct payroll and any other financial transactions on a computer that was used only for that one purpose–turned on, transaction completed, turned off. No Internet, no email checking, nothing. The finance director said it was too much trouble.
jl
@japa21: Don’t need a source. It can be dismissed out of hand. It is patent nonsense. If the source of the info is sincere, maybe they will try to provide a non-garbled version that makes some sense.
Adam L Silverman
@BR: The only way to change the coverage is to make it unprofitable. That means getting the advertisers to stop advertising because they believe being associated with the broadcast, what is being broadcast, and how it is being broadcast, will hurt their bottom line. The only thing that network and cable news, talk radio news and commentary, and the print media and everything that’s branched onto the Internet is concerned with is eyeballs on advertising. That’s what makes it money. If you want them to change you have to hurt them where it counts: the pocket book.
Adam L Silverman
@Gin & Tonic: https://www.youtube.com/watch?v=AOGO6nyonWI
jl
Regarding subject of this post, I was disgusted, alarmed and disturbed that Trump’s dangerous and irresponsible comments about NATO didn’t even get a mention in the news this morning. Corporate media truly worthless.
I am like Josh Marshall at TPM. I have had serious doubts about the wisdom of the way NATO has been expanded, and think a serious policy debate is needed about what a post Cold War European and Russian security arrangement should look like. Good case can be made that our approach to NATO is outdated and it needs to change.
But, once the treaties are signed, they have to be honored. Rashly saying that we will ‘walk away’ and use the treaty commitments as a bargaining chip in some confused and idiotic power play over money is irresponsible. And this is not a news story for the media. Unbelievable. Trump is very dangerous.
Hope the Dem convention slams Trump and Trump good on foreign policy and national security during prime time. I guess Bill Clinton Obama and Biden are the ones to do it.
Adam L Silverman
@efgoldman: That’s because:
https://www.youtube.com/watch?v=Dz0egrNk83U
burnspbesq
@? Martin:
It may be papered like debt, but it’s convertible into equity. They think they invested in owning the White House.
jl
@Quinerly: MSNBC is cynically cherry picking to juice controvery and their pundit narratives, and it is disgraceful.
Get on youtube and you can see interviews with sensible and rational HRC and Sanders delegates, from of all places, The Young Turks, an anti-Hillary fever swamp. Yes, some of the big network and cable outfits are worse for actual news than a crazed and panicked fever swamp of Benie fanatics.
Adam L Silverman
@jl: NATO expansion and maintenance is another post. We’ll get back to you!
jl
@Adam L Silverman: Since our news media apparently doesn’t think it is an important issue, maybe a little compare and contrast about the right versus wrong ways to fix any complaints about treaty commitments in order.
SoupCatcher
@? Martin:
The CA Secretary of State puts out a document on the voting systems in use by county (warning: PDF link) for each election. It’s about as ugly as you would expect – at least five different vendors with multiple models of equipment.
eta You can also sign up to get voting system announcements via email. Yay?
Raven Onthill
I don’t have a lot of time to write about this (I am busy with other things.) I will shortly remark that our civilian network infrastructure is vastly insecure, and this is due to simple irresponsibility on the part of major software vendors, as well as active efforts on the part of the various agencies like the NSA, CIA, and so on to make the public more easily subject to surveillance. As security experts have been telling us for over 20 years, once a “back door” (as the experts call it) is created, it is impossible to know who will walk through it.
Adam L Silverman
@Raven Onthill: Looking forward to it.
SiubhanDuinne
@jenn:
At the very least, you’d think he could have waited to announce this until after the inauguration. Or at least the election. Or even the end of Convention Week. But no, he used the Democratic Party for his own selfish purposes and then crumpled it up and tossed it aside like a snotty Kleenex.
Last night, listening to his speech, I was inclined to cut him some slack, but no more. Fool me twice….
Steve in the ATL
@patrick II: There has never been any question in my mind that Bush stole Ohio. The CEO of Diebold and the Ohio SOS both promised in advance to deliver the state to him.
SiubhanDuinne
@efgoldman:
He’s not even up for reelection until 2018. He could so easily have waited a few months and at least played the role of a loyal Democrat through the election, but I guess that would contaminate his fucking purity.
jl
@SiubhanDuinne: Vermont doesn’t have partisan registration, so what could that rumor be about? It sounds like nonsense to me.
Mister Forkbeard
@Quinerly: Someday, someone will have to explain how exactly the DNC and HRC sabotaged Bernie and cheated in the election. I have yet to get a non-conspiracy-theory, even after the e-mail release this last weekend.
J R in WV
@? Martin:
Access and turnout makes no never mind if the results are determined by people paid to provide necessary and specified results no matter how voters actually cast those multi-lauguage ballots.
Mister Forkbeard
@SiubhanDuinne: I’m not hearing a thing about this anywhere. I would really wait for confirmation, since it would be a huge dick move to make during the actual convention and directly contradict everything he was saying in his speech last night.
evgen
@Sam: The best running commentary over the past few weeks on attribution of the DNC dump was from @PwnAllTheThings on twitter. It was a laugh riot to watch these hackers get their opsec owned completely by the infosec community. The hackers were absolutely Russian, no doubt whatsoever. That they were state-sponsored is a bit fuzzier, but the techniques used match those of other state-sponsored Russian hackers. Whether or not Putin was actually choosing the target and end-game is pure speculation.
Original Lee
@Mnemosyne: I don’t mind It’s a Small World. I once rode it 10 times in a row with one of my nieces because it was the only ride she wanted to be on.
Although I had the song as an earworm for days afterwards, it was worthwhile to have watched her little face light up every single time.
kdaug
@Anoniminous: There’s a reason our nukes run on 5 1/4 floppies
chopper
@Hunter Gathers:
a-yup. and 40+% of the country is gonna vote for this schlemiel.
Mandalay
@Adam L Silverman:
You are linking to articles that assert as fact that “Russian Intelligence” (or “the Russian government” or “Putin” or “the Russians” – pick your moniker) hacked the DNC without any hard evidence, and you make the same mistake in your own comments.
Nobody – repeat nobody – has produced any solid evidence that the hacking was done by the Russian government. The strongest claim that it was has been made by CrowdStrike, the firm that the DNC paid to research the hacks into their system, and it is very convenient for them both (for different reasons) to conclude that it was the Russian government. But if you closely scrutinize the details of the claims made by CrowdStrike they have no real evidence at all that the Russian government was responsible.
The nonsense has now been whipped up into a frothy mess. Some security firms speculate or guess that it might be the Russians, and then the media pounces, and then politicians start cherry picking from the media articles. Of course it may have actually been the Russian government who hacked the DNC, but there are tens of thousands of hackers trying to break systems all over the world all the time. There no reason it has to be the Russians at all.
I’m very surprised to see you so casually asserting that the Russian government is responsible at this stage. You have no real evidence for that being true at all….just a load of links to articles that also provide no real evidence.
ETA Also see post#185 by evgen: “Whether or not Putin was actually choosing the target and end-game is pure speculation.”
Mandalay
@evgen: This.
Imagine a Russian site gets hacked, and there is evidence that Americans hacked them. Would it then be reasonable to automatically assume that the hackers were the US government, or agents of the US government? Of course not.
The Fat Kate Middleton
@singfoom: Wow. I can’t stop watching this.
Raven Onthill
@Adam L Silverman: Thank you. Still don’t have the hours it would take to cover this ground fully – would you believe I’m working on a “Origins of the second amendment” article? – and by the time that is done discussion will have moved on. Meantime, though, here’s real security expert Bruce Schneier’s links post on the subject. There is a link to an overview of what has been discovered and another on its political and national security implications. Some good comments, some annoying.
As to the broader issues, I can also say that passwords by themselves are at best a medium security technology and more usually low security; at least we ought be using some form of two-factor authentication in anything we care about, and this includes all our business transactions (including banking, yes) and all our official business, e-mail encryption ought to be routine, and most medical records ought to be encrypted. At the same time, excellent key escrow systems are needed to avoid the loss of encrypted data.
The agency that has the job of securing US electronic communications is The Agency: the NSA, but so far they seem more interested in being able to break into other people’s communications than securing them.
polyorchnid octopunch
In Canada, all our elections are done with paper ballots counted by a small army of humans. This makes our elections extremely difficult to hack. If you want to make sure that your elections are unhackable, this is the best way to do it.
The process here is this: everyone gets a paper ballot, they mark it with a pencil. At the end of the day, for each election (there is one in every riding in Canada for the MP for that riding), each ballot is examined by n+1 (where n is the number of candidates in the election; these people are referred to as scrutineers) people, the +1 being the poll clerk, a non-partisan position staffed by a special government agency called Elections Canada. If there is a dispute about the marking, that ballot is set aside into a special box for disputed ballots, while spoiled ballots (my personal fave from when I was a poll clerk was someone who wrote “I think you all suck” on a ballot) are put into a separate box for spoiled ballots. After the count is tabulated, the boxes are all sealed and sent to the Returning Office for the riding. There the counts are tabulated along with the number of votes to look for discrepancies. If discrepancies are found, the offending ballot box is opened up and the ballots are again counted by n+1 people, and then resealed.
Yes, this process is extremely labour intensive, and yes it’s extremely inefficient compared to machines, tabulators, etc, but it also makes elections damn near unstealable.
While commerce always seeks more efficiency, it turns out there are important processes where efficiency is far from the highest priority. Elections is one of those processes.
bemused senior
@Raven Onthill: The FFIEC has required two factor authentication for online banking login since 2007. They now require it on a finer grained level. The second factor was often a software token on the machine used to access the account bound to characteristics of the machine. Failure to match leads to a challenge question. Now often will provide hardware tokens for your account for a small fee.
Adam L Silverman
@Raven Onthill: Where are you doing the 2nd Amendment article for? I’m in the middle of reading A Well Regulated Militia: The Founding Fathers and the Origin of Gun Control in America by Saul Cornell. I’ve got his The Second Amendment on Trial cued up after that. I’ve already made it through Winkler’s Gun Fight on the Heller decision and Waldman’s The Second Amendment: A Biography.
Adam L Silverman
@Mandalay: You were saying?
http://www.nytimes.com/2016/07/27/us/politics/spy-agency-consensus-grows-that-russia-hacked-dnc.html
wjs
@Mandalay: You forget that they have the guy in custody. He’s sitting in jail in Northern Virginia. At some point, he’s probably going to cut a deal.
Nervous yet? Maybe you should be.
In the real world of budgets, priorities, and defense procurement, we have the US Cyber Command. In order to justify its existence, increase funding to the programs it administers, and win the hearts and minds of the oversight people in Congress, they are likely executing a plan to deal with all of this.
Nervous yet? Maybe we all ought to be.
dianne
I read an article recently about encryption software that could have been installed on the DNC computers easily enough. I don’t know if it would have prevented the hack but, Jesus, why not at least put up another small roadblock
that might have saved themselves some of this torment. I’m waiting for the hack on the IRS of some time ago to finally release Trump’s returns since he never will. Maybe some friendlies will hack the hackers. The Rs are all spinning like dervishes to make this seem like no big deal. They’ve turned on a dime – all those cold warriors have turned luke warm.
michelle
@Adam L Silverman: You’re welcome! Like Richard Mayhew, you have the rare ability to take complex subjects and express them in a way that is clear and comprehensible. I emailed Alain and Cole this morning.
Richard Mayhew
@michelle: You make me blush
moops
For the technically interested I can provide further reading from people I like
http://arstechnica.com/security/2016/07/clinton-campaign-email-accounts-were-targeted-by-russians-too/
long form article that summarized previous Ars Technica reporting, and adds the Yahoo component.
As for encryption, a little is worse than useless. Encryption done correctly has a small but noticeable burden on the user. It cannot be avoided. There are actually proofs of this property.
Turnkey/automatic/invisible encryption systems are like crack cocaine to state-sponsored level hacking. they are almost universally have one of the following flaws: misconfigured, compromised from the source, have flawed key management, are still vulnerable to phishing attacks, fail completely once they fail partially, and on and on.
You have to adopt a secure mindset to have security. If you are doing opposition research for a US presidential campaign, you might have to view secrecy as valuable and worth the time and effort thinking about it and acting on it implies.
Name
– multifactor authentication
– limited services
– include social engineering “testing” with periodic testing.
michelle
@Richard Mayhew: I’ve been told that before :)