I’ve exhausted my WaPo views for the month and am too lazy to jettison my cookies to hop over the firewall, but according to MSNBC, Bart “Not-Greenwald” Gellman and Ashkan “Not-Poitras” Soltani published an NSA bombshell today:
The Washington Post reported Wednesday that the NSA hacked into the data centers of Yahoo and Google – two of the biggest email and cloud storage providers. It cites documents leaked by former NSA contractor Edward Snowden.
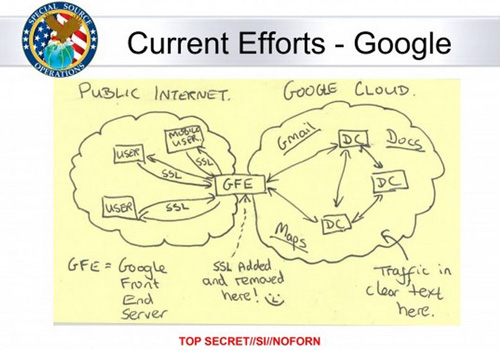
According to WaPo, the hacking was accomplished using an NSA tool called MUSCULAR. If you think that’s a stupid name, wait until you see the “Google Cloud Exploitation” slide that describes it from the NSA presentation, which I managed to snatch off the WaPo site before they gave me the bum’s rush:
Sweet cartwheeling Jesus. While we technologically inept folks await a verdict on whether this latest “bombshell” is a nothingburger or somethingsalad, can we just pause a moment and reflect on the implications of this toddler-level depiction of the possibly monstrous privacy destructorator? Here’s an illustration of our collective pause, which was created in PowerPoint and Paint in three minutes flat by my dumbest chicken:
I’ll back her up against the NSA graphic design team any fucking day.
Now, on to weightier matters. It has been suggested in alternate quarters that your Balloon Juice team is a frivolous, feckless flock of fooking trolls, authoritarianism aficionados and bitter PUMA cat ladies who are not a’tall interested in a rational discussion of the true issues surrounding surveillance and security.
This is 100% true. However, just yesterday, valued commenter Jockey Full of Malbec, who has excellent taste in wine and is therefore trustworthy, did suggest some questions that could lead to a rational discussion:
(1) What level of secrecy WOULD be acceptable to you?
(2) What checks and balances would you like to have that are NOT currently in place?
(3) What concrete legislation would you propose to achieve (1) and (2)?
(4) Which elections in 2014 and 2016 should sympathetic Democrats target to achieve (3)?
And equally valued commenter Omnes Omnibus elaborated upon JFOM’s suggestions in that same thread with the following:
I would suggest adding: “How much surveillance is acceptable?”, “What types? Metadata, e-mail content, phone locations, phone conversations, CCTV?”, and “What should be the standard for allowing the surveillance? Probable cause, reasonable suspicion, etc.?”
Moreover, your humble correspondent brought up proposed legislation that was once entertained in the US Congress and begged for your insights just a few days ago, albeit in the middle of an NSA thread that reached .5 TBogg proportions, which is akin to farting in a whirlwind (i.e., not very ladylike). Anyhoo, here’s that:
So the question becomes, what are the proper limits? What constitutes adequate control? Here are some proposals entertained in Congress:
Restrict or end bulk records collection and limit surveillance to individuals who merit surveillance due to probable cause
Require government analysts to get court approval before accessing incidentally collected data from Americans
Require executive branch reports to Congress on how many American communications are swept up during surveillance
Require the DOJ to produce a public report giving aggregate data on how many people have been targeted for surveillance
Restrict the use of gag orders related to surveillance court orders (see FISA Court motions by Google and Microsoft)
Declassify significant surveillance court opinions, with redactions as necessary, of course
What do you think? Are these sensible? Too restrictive of government surveillance powers? Do they not go far enough?
What say you?
NSA is all up in your LOLCATS for real, says WaPo bombshellPost + Comments (140)